|
|
在SDK中有一个工具依赖性查找工具depends.exe可以看到进程的子系统类型。发现这个工具和VS6企业版中的MicrosoftVisualStudio6.0Tools中的Depends("C:\ProgramFiles\MicrosoftVisualStudio\Common\Tools\DEPENDS.EXE")是一样的。晕!!
Windows子系统:
1、环境子系统csrss.exe包括下列支持:
a)控制台文本窗口
b)创建或删除进程和线程
c)对16位虚拟DOS机进程的一部分支持
d)其他一些函数,比如gettempfile,definedosdevice,exitwindowsex等
2、内核模式设备驱动程序win32k.SYS包含:
a)窗口管理器,包括采集键盘,鼠标的输入
b)图形设备接口GDI(在NT4之前,作为用户模式windows子系统的一部分)
3、子系统DLL比如kernel32.DLL,advapi.DLL,user32.DLL,GDI32.dll
4、图形设备驱动程序
将USER和GDI放在内核模式中,windows会不稳定吗?
答:在此NT4之前,一个错误指针会导致系统崩溃,将窗口管理器和GDI从用户模式迁移到了内核模式,不仅提高了性能,而且可以将稳定性降到最低!
Posix子系统
一个基于UNIX的可移植的操作系统接口的首字母缩写,这个POSIX标准有很多,Windows实现的是POSIX.1
POSIX子系统有助于将UNIX应用移植到windows平台上,然而,这个程序仍然被链接为可执行程序,不能调用windows函数。如果你需要unix移植到windows中并且可以调用windows函数,你需要购买UNIXTOWINDOWS的软件,比如www.MKSSOFTWARE.COM
如果要在windows编译链接一个posix程序,需要在SDK的中POSIX头文件和库文件中使用链接库psxdll.DLL。
OS/2子系统
支持有局限,如果OS/2中设计的硬件及高级视频IO代码,在windows上使用该子系统不可用。
原生的OS/21.2上有16M的内存限制。而在windows提供的OS/2中可以使用512M
硬件抽象层HAL
C:\WINDOWS\DriverCache\i386>dir
驱动器C中的卷没有标签。
卷的序列号是18F6-A188
C:\WINDOWS\DriverCache\i386的目录
2011-12-0510:36<DIR>.
2011-12-0510:36<DIR>..
2008-04-1420:0062,857,674driver.cab
2个文件83,085,231字节
2个目录146,253,623,296可用字节
如果打了SP3补丁,则在此CAB压缩包中有多个版本的HAL.DLL文件
C:\>dirntoskrnl.exe/a/s
驱动器C中的卷没有标签。
卷的序列号是18F6-A188
C:\WINDOWS\system32的目录
2008-04-1420:002,144,768ntoskrnl.exe
1个文件2,144,768字节
所列文件总数:
1个文件2,144,768字节
0个目录146,251,362,304可用字节
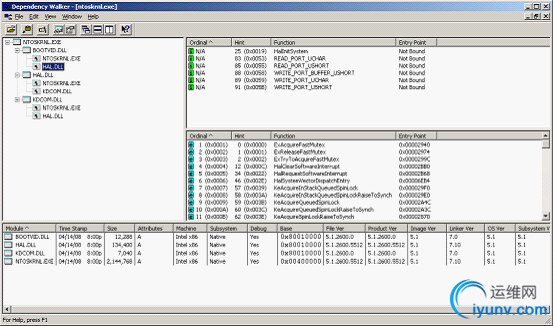
其中,我们发现ntoskrnl链接了HAL,HAL又链接了ntoskrnl,相互使用了对方的函数。Ntoskrnl也链接了BOOTVID.DLL,这个是用来实现GUI启动屏幕的引导视频驱动程序,在XP系统以后的环境中还有一个附加的DLL,kdcom.DLL它包含了内核调试器的基础代码,在XP之前,它被包含在ntoskrnl.EXE中。
从WINDOWS2000开始使用WDM驱动也就是windows驱动程序模型。从WDM来看,有三种驱动程序
1、总线型驱动:总线控制器,适配器,桥,带有子设备的设备提供服务器。比如PCI,USB等
2、功能性驱动:这个是必须的,比如SCSI
3、过滤性驱动,一般只有OEM来提供放在总线型驱动之上。
C:\>pstat|more
Pstatversion0.3:memory:2882732kbuptime:03:33:12.531
nopagefilesinuse
Memory:2882732KAvail:1809228KTotalWs:808476KInRamKernel:2580KP:59176K
Commit:872612K/718480KLimit:2720228KPeak:936212KPoolN:48464KP:59484K
UserTimeKernelTimeWsFaultsCommitPriHndThdPidName
1699962309601FileCache
0:00:00.0006:19:14.04628000020IdleProcess
0:00:00.0000:02:03.82834413635528798874System
0:00:01.0150:00:00.03149632823211193612smss.exe
0:00:01.7650:00:12.4211058431486234013751131124csrss.exe
0:00:00.1400:00:00.31253005907813613526231156winlogon.exe
0:00:00.6560:00:01.79635801557818449321151200services.exe
0:00:01.6400:00:03.76513081679828409425161212lsass.exe
0:00:41.2340:00:08.625154605338171233008181331392avguard.exe
0:00:00.0460:00:00.015247665268883321572avshadow.exe
0:00:00.0460:00:00.15634169122076810041592ati2evxx.exe
0:00:00.0620:00:00.0465556174632408226181612svchost.exe
0:00:00.2340:00:00.2655024165220648351101672svchost.exe
0:00:00.5780:00:00.890390425888223681125128ati2evxx.exe
0:00:01.4210:00:01.0932184414256134688151657676svchost.exe
0:00:04.5000:00:00.65644007844203281076812svchost.exe
--More--
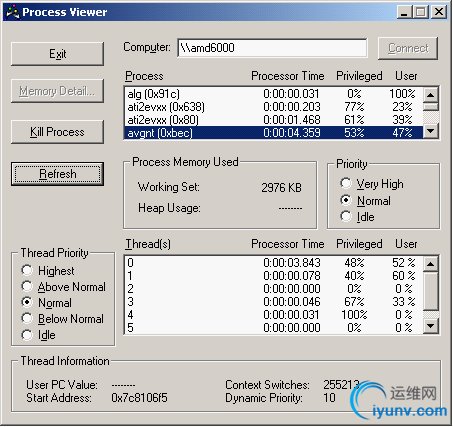
System进程在windows2000中ID=8,在windowsxp和2003中,ID=4
C:\>livekd
LiveKdv5.0-Executekd/windbgonalivesystem
Sysinternals-www.sysinternals.com
Copyright(C)2000-2010MarkRussinovichandKenJohnson
LaunchingC:\ProgramFiles\DebuggingToolsforWindows(x86)\kd.exe:
Microsoft(R)WindowsDebuggerVersion6.12.0002.633X86
Copyright(c)MicrosoftCorporation.Allrightsreserved.
LoadingDumpFile[C:\WINDOWS\livekd.dmp]
KernelCompleteDumpFile:Fulladdressspaceisavailable
Comment:'LiveKDlivesystemview'
Symbolsearchpathis:srv*c:\Symbols*http://msdl.microsoft.com/download/symbols
Executablesearchpathis:
WindowsXPKernelVersion2600(ServicePack3)MP(2procs)Freex86compatible
Product:WinNt,suite:TerminalServerSingleUserTS
Builtby:2600.xpsp.080413-2111
MachineName:
Kernelbase=0x804d8000PsLoadedModuleList=0x8055e720
Debugsessiontime:SunFeb1310:34:57.89717420(UTC+8:00)
SystemUptime:0days3:40:13.673
WARNING:Processdirectorytablebase00722000doesn'tmatchCR30A9F06C0
WARNING:Processdirectorytablebase00722000doesn'tmatchCR30A9F06C0
LoadingKernelSymbols
...............................................................
................................................................
............
LoadingUserSymbols
Loadingunloadedmodulelist
...............
0:kd>0:kd>0:kd>
0:kd>
0:kd>!stacks0
Proc.Thread.ThreadTicksThreadStateBlocker
***ERROR:ModuleloadcompletedbutsymbolscouldnotbeloadedforLiveKdD.SYS
[8a36ba00System]
4.00004c8a362020ffffef52Blockednt!MiGatherPagefilePages+0x40
***ERROR:Moduleloadcompletedbutsymbolscouldnotbeloadedforsptd.sys
4.0000648a392bd800ce2c2Blockedsptd+0x874ee
4.0000688a39296000ce74fBlockedsptd+0x874ee
4.00006c8a3926e800ce74fBlockedsptd+0x874ee
***ERROR:ModuleloadcompletedbutsymbolscouldnotbeloadedforRtkHDAud.sy
s
4.00016c89d3cb0800ce5fcBlockedRtkHDAud+0x110e
4.00017089d3c89000ce5fcBlockedRtkHDAud+0x110e
4.00017489cc686800ce5fcBlockedRtkHDAud+0x110e
4.00017889cbdb0800ce5fcBlockedRtkHDAud+0x110e
4.00017c89cbcda800ce5fbBlockedRtkHDAud+0x110e
4.00018089cbc89000ce5fbBlockedRtkHDAud+0x110e
4.0001848a06f6e800ce5fbBlockedRtkHDAud+0x110e
4.00018889cbf7e8ffffe699BlockedRtkHDAud+0x110e
4.00018c89cbf5480004025BlockedRtkHDAud+0x49368
4.00019089cca5280003f4cBlockedRtkHDAud+0x43c98
!stacks0可以表示出system进程中的系统线程,可以找出一个线程的当前地址
!Drivers可以列出每个已经被加载的设备驱动程序的基础地址
第一列表示进程ID和线程ID
第二列表示线程的当前地址
第三列表示线程是wait状态还是就绪状态,还是运行状态,还是运行状态
第四列表示该线程的堆栈中最顶上的地址,可以看出每个线程是哪个驱动程序中被启动起来的。
s
4.0005ac87cb346800c0e87Blockedavgntflt+0x16a8
4.0005b087cb31f00000082Blockedavgntflt+0x19ab
***ERROR:Moduleloadcompletedbutsymbolscouldnotbeloadedforhcmon.sys
4.0000c087a0772000cd9c8Blockedhcmon+0x1b7d
***ERROR:Moduleloadcompletedbutsymbolscouldnotbeloadedforvmx86.sys
4.0000d487bc13c800cd9c6Blockedvmx86+0x3a9d
4.000d2487a25020fffff285BlockedHTTP!UlpScavengerThread+0x5d
***ERROR:ModuleloadcompletedbutsymbolscouldnotbeloadedforPECKP.SYS
4.000da0878737f000c1ed7BlockedPECKP+0x1234a
[899a3370smss.exe]
***ERROR:Moduleloadcompletedbutsymbolscouldnotbeloadedforati2mtag.sy
s
[88242da0csrss.exe]
464.000470884046e800ce2c8Blockedati2mtag+0x4b1c
464.00047c88229da8ffffffe1Blockednt!KiFastCallEntry+0xfc
464.00048c88400d10ffffd5a6Blockednt!KiFastCallEntry+0xfc
464.0004948821da30ffffd59bBlockedwin32k!xxxMsgWaitForMultipleObjects+0x
b0
464.0004f487ce45f0ffffb3c5Blockednt!KiFastCallEntry+0xfc
464.000ff08799abf8ffffb3b4Blockednt!KiFastCallEntry+0xfc
[88412470winlogon.exe]
484.0004ac8821cda8ffffd639Blockednt!KiFastCallEntry+0xfc
484.0007fc87c11270000003bBlockednt!KiFastCallEntry+0xfc
484.0003b887bde408ffffba64Blockednt!KiFastCallEntry+0xfc
484.000ba887cd3798ffffb995Blockednt!KiFastCallEntry+0xfc
484.00084c87ae9020ffffb94bBlockednt!KiFastCallEntry+0xfc
484.000cec8749eda8ffffbc62Blockednt!KiFastCallEntry+0xfc
484.00078487986bf000000fbBlocked
TYPEmismatchforthreadobjectat87436640
484.------NOETHREADDATA
484.------NOETHREADDATA
Unabletoread_ETHREADatfffffe50
[8821b410services.exe]
4b0.0004cc87cfcb30ffffb875Blockednt!KiFastCallEntry+0xfc
4b0.00052c87ccf5d8ffffbc7cBlockednt!KiFastCallEntry+0xfc
4b0.00054087cd1020ffffb3e1Blockednt!KiFastCallEntry+0xfc
4b0.00054c87650020ffffb360Blockednt!KiFastCallEntry+0xfc
4b0.000cac87695020ffffb35fBlockednt!KiFastCallEntry+0xfc
[87cf3418lsass.exe]
4bc.0004dc87cf05f0ffffb5c0Blockednt!KiFastCallEntry+0xfc
4bc.0004f087ce4868ffffbc70Blockednt!KiFastCallEntry+0xfc
4bc.0005088821ebb8ffffd5cdBlocked+0x8821ebb8
4bc.00052887cd6da8ffffb74aBlockednt!KiFastCallEntry+0xfc
[87cbfb38avguard.exe]
570.0005a487cc1da8ffffb3a3Blockednt!KiFastCallEntry+0xfc
570.0005b487cafcd0ffffb35bBlockednt!KiFastCallEntry+0xfc
570.0005b887c9f8f0ffffb333Blockednt!KiFastCallEntry+0xfc
570.0005bc87ca94e8ffffb330Blockednt!KiFastCallEntry+0xfc
570.0005dc87c9dda8ffffb721Blockednt!KiFastCallEntry+0xfc
570.0005e487cc3b10ffffb392Blockednt!KiFastCallEntry+0xfc
570.0005ec87c68020ffffb5edBlockednt!KiFastCallEntry+0xfc
570.0005f487ca0458ffffb46dBlockednt!KiFastCallEntry+0xfc
570.0005fc87c8e338ffffb5b7Blockednt!KiFastCallEntry+0xfc
570.00060087c67718ffffb344Blockednt!KiFastCallEntry+0xfc
[87c56be0avshadow.exe]
[87c52420ati2evxx.exe]
[87c38320svchost.exe]
64c.00067887c284e8ffffb536Blockednt!KiFastCallEntry+0xfc
64c.00076c87ae28680001208Blockednt!KiFastCallEntry+0xfc
64c.0003588a277be80001208Blockednt!KiFastCallEntry+0xfc
64c.000764878f1da80001208Blockednt!KiFastCallEntry+0xfc
64c.00042c878f1b300001208Blockednt!KiFastCallEntry+0xfc
64c.00032487ae20200001208Blockednt!KiFastCallEntry+0xfc
64c.00031c87ae25f00001208Blockednt!KiFastCallEntry+0xfc
64c.0007b08a2763280000001Blockednt!KiFastCallEntry+0xfc
64c.000834878f05380001208Blockednt!KiFastCallEntry+0xfc
64c.0001d487662020ffffbb8cBlockednt!KiFastCallEntry+0xfc
[87c28be0svchost.exe]
688.000eec878e8020ffffb2afBlockednt!KiFastCallEntry+0xfc
688.000fa88768f020ffffb2adBlockednt!KiFastCallEntry+0xfc
688.000dcc8747ada8ffffb85fBlockednt!KiFastCallEntry+0xfc
[87c0da20ati2evxx.exe]
80.0003cc87bdcda8ffffb3f9Blockednt!KiFastCallEntry+0xfc
[87c02020svchost.exe]
2a4.0002a087c100200001208Blockednt!NtReadFile+0x55d
2a4.00032087bf25c80001208Blockednt!KiFastCallEntry+0xfc
2a4.0003e087bd9718ffffb91bBlockednt!KiFastCallEntry+0xfc
2a4.0003e887be45a80001208Blockednt!KiFastCallEntry+0xfc
2a4.0003f887bd5020000041cBlockednt!KiFastCallEntry+0xfc
2a4.00060887bd7da80001208Blockednt!KiFastCallEntry+0xfc
2a4.000658884240200001208Blockednt!KiFastCallEntry+0xfc
2a4.0006f887a0daa0ffffdb0fBlockednt!KiFastCallEntry+0xfc
2a4.0000b887bccda800000ddBlockednt!KiFastCallEntry+0xfc
2a4.0000b087bcea38ffffffebBlockednt!KiFastCallEntry+0xfc
2a4.0000b487a1bc40ffffe194Blockednt!KiFastCallEntry+0xfc
2a4.000534879288300000050Blockednt!KiFastCallEntry+0xfc
2a4.000a2887ae7bf8ffffb4d8Blockednt!KiFastCallEntry+0xfc
2a4.0008e087ae4270ffffb64cBlockednt!KiFastCallEntry+0xfc
2a4.0008e48795f2a0ffffb64cBlockednt!KiFastCallEntry+0xfc
2a4.0008e887ae23780001208Blockednt!KiFastCallEntry+0xfc
2a4.0009408a2738680001208Blockednt!KiFastCallEntry+0xfc
2a4.0009788a2725d80001208Blockednt!KiFastCallEntry+0xfc
2a4.0009948a2716d00001208Blockednt!KiFastCallEntry+0xfc
2a4.000be087c78da8ffffb4d9Blockednt!KiFastCallEntry+0xfc
2a4.000ee48a2b95000000975Blockednt!KiFastCallEntry+0xfc
2a4.0003f487875020ffffd71dBlockednt!KiFastCallEntry+0xfc
2a4.0009e48780c610ffffb22aBlockednt!KiFastCallEntry+0xfc
[87bf2348svchost.exe]
32c.000c388766ada8ffffb30dBlockednt!KiFastCallEntry+0xfc
32c.000b988764c3a0ffffb2e9Blockednt!KiFastCallEntry+0xfc
32c.000b3c87685020ffffb2e9Blockednt!KiFastCallEntry+0xfc
[87be5be0svchost.exe]
390.00036087756c10ffffb718Blockednt!KiFastCallEntry+0xfc
[87bd56a0sched.exe]
664.0006ac87bce5c80001208Blockednt!NtReadFile+0x55d
664.0006b087bc9be80001208Blockednt!KiFastCallEntry+0xfc
664.0006b887bce3500001208Blockednt!KiFastCallEntry+0xfc
664.0006d087bd6c40000017dBlockednt!KiFastCallEntry+0xfc
[87a135a0inetinfo.exe]
104.00010887bc8a680001208Blockednt!NtReadFile+0x55d
104.00013087a0abe8ffffd921Blockednt!KiFastCallEntry+0xfc
104.00079c8799d470ffffb3b7Blockednt!KiFastCallEntry+0xfc
104.00038887996438ffffb492Blockednt!KiFastCallEntry+0xfc
104.0003bc879a4a500001208Blockednt!KiFastCallEntry+0xfc
104.0003c087b45da8ffffb478Blockednt!KiFastCallEntry+0xfc
[879fe988jqs.exe]
120.000134884265e80001208Blockednt!KiFastCallEntry+0xfc
120.00014487a104f8000028bBlockednt!MiDeferredUnlockPages+0x31
120.0001d8879f2c18ffffb193Blockednt!KiFastCallEntry+0xfc
[879e6020sqlservr.exe]
1bc.0002b087b86538ffffb235Blockednt!KiFastCallEntry+0xfc
1bc.0002f087b77020ffffb1edBlockednt!KiFastCallEntry+0xfc
[87b896a0sqlwriter.exe]
22c.000230879ddda80001208Blockednt!NtReadFile+0x55d
22c.000234879d79700001208Blockednt!KiFastCallEntry+0xfc
[879dfbe8vmware-authd.ex]
25c.000d4c87be03280000076Blockednt!KiFastCallEntry+0xfc
25c.000d5087bcb0200001208Blockednt!KiFastCallEntry+0xfc
25c.000d5487bcbda80001208Blockednt!KiFastCallEntry+0xfc
25c.000f9087b63970ffffb2ccBlockednt!KiFastCallEntry+0xfc
[879c8da0vmount2.exe]
2f8.00033887b71020ffffb265Blockednt!KiFastCallEntry+0xfc
[879bcda0vmnat.exe]
[879ae4e0vmnetdhcp.exe]
[87a5d4e0explorer.exe]
a88.000ae087b03da80000b69Blockednt!KiFastCallEntry+0xfc
a88.00085087c0a020ffffb44bBlockednt!KiFastCallEntry+0xfc
a88.0001ec87ade6b0000054fBlockednt!KiFastCallEntry+0xfc
[87b20880RTHDCPL.EXE]
[8796fbe0MOM.exe]
b1c.000b3487a36da80001208Blockednt!KiFastCallEntry+0xfc
b1c.000fec87b6fda8ffffb268Blockednt!KiFastCallEntry+0xfc
b1c.00044487978c00ffffb3a2Blockednt!KiFastCallEntry+0xfc
b1c.0004588823f3280001208Blockednt!KiFastCallEntry+0xfc
b1c.00045c8823d0200001208Blockednt!KiFastCallEntry+0xfc
b1c.0008a087ae8da8ffffb37bBlockednt!KiFastCallEntry+0xfc
TYPEmismatchforthreadobjectat87642020
b1c.------NOETHREADDATA
TYPEmismatchforthreadobjectat8a308140
b1c.------NOETHREADDATA
b1c.------NOETHREADDATA
Unabletoread_ETHREADat85ffe53
[8796cb40GooglePinyinDae]
b2c.000b608a1bc4c00001208Blockednt!KiFastCallEntry+0xfc
b2c.000b648a1bc8a80001208Blockednt!IopXxxControlFile+0x5c5
b2c.000b68884052c0ffffd9aeBlockednt!KiFastCallEntry+0xfc
b2c.000bc487bd0bf800002eeBlockednt!KiFastCallEntry+0xfc
b2c.000de0876ad020ffffb14fBlockednt!KiFastCallEntry+0xfc
[88406da0SetPoint.exe]
b7c.00043487cb5be80001208Blockednt!KiFastCallEntry+0xfc
b7c.0006448a2bb9f80001208Blockednt!KiFastCallEntry+0xfc
[87bb84c8avgnt.exe]
bec.000d0887cb0a300001208Blockednt!KiFastCallEntry+0xfc
[87970418GooglePinyinSer]
[87b23da0ctfmon.exe]
c24.000c2887bf9618ffffb2e9Blockednt!KiFastCallEntry+0xfc
[87be14e0YodaoDict.exe]
d44.0002288a2bc86800000c0Blockednt!KiFastCallEntry+0xfc
d44.000f8487960020ffffb25eBlockednt!KiFastCallEntry+0xfc
d44.0009608a2757480001208Blockednt!KiFastCallEntry+0xfc
d44.000a608a2708b8ffffb0adBlockednt!KiFastCallEntry+0xfc
d44.000a6488235bf80001208Blockednt!KiFastCallEntry+0xfc
[87cfba30vmserverdWin32.]
d5c.000fe487c3cda8ffffb378Blockednt!KiFastCallEntry+0xfc
d5c.0007b887b44bf0ffffb7acBlockednt!KiFastCallEntry+0xfc
d5c.000ea887964bf0ffffb2e2Blockednt!KiFastCallEntry+0xfc
[879c0be0YoudaoNote.exe]
db4.00043c87a174800000610Blockednt!KiFastCallEntry+0xfc
db4.00085c87c98da80001208Blockednt!KiFastCallEntry+0xfc
db4.0008fc8a2779700001208Blockednt!KiFastCallEntry+0xfc
db4.00098087add4600001208Blockednt!KiFastCallEntry+0xfc
[88411020klive.exe]
df8.000ff487bcbb300001208Blockednt!KiFastCallEntry+0xfc
df8.000ff8884113400001208Blockednt!KiFastCallEntry+0xfc
df8.000d9487acf850ffffb111Blockednt!KiFastCallEntry+0xfc
df8.000fcc87bcaa380001208Blockednt!IopXxxControlFile+0x5c5
df8.0000d88799f3980001208Blockednt!IopXxxControlFile+0x5c5
df8.0000ec89c46aa00001208Blockednt!IopXxxControlFile+0x5c5
df8.000de487aafa78ffffb069Blockednt!KiFastCallEntry+0xfc
df8.000e9488402868ffffd5a9Blocked+0xa3f5ecec
df8.000a6c8781d868ffffb2ecBlockednt!KiFastCallEntry+0xfc
df8.0008f487aa7da8ffffb03fBlockednt!KiFastCallEntry+0xfc
df8.000594878a0a28ffffb04dBlockednt!KiFastCallEntry+0xfc
df8.0009fc8789f980ffffb449Blockednt!KiFastCallEntry+0xfc
df8.000a048789f490ffffb416Blockednt!KiFastCallEntry+0xfc
df8.000a548794f710ffffb06dBlockednt!KiFastCallEntry+0xfc
df8.000f3487a0a870ffffd9acBlockednt!KiFastCallEntry+0xfc
df8.000b28877f1b380001208Blockednt!KiFastCallEntry+0xfc
[87a53408CCC.exe]
414.00034c8796b4e0ffffb11bBlockednt!KiFastCallEntry+0xfc
414.00024087b6cc48ffffb341Blockednt!KiFastCallEntry+0xfc
414.00012c87436b30ffffb5c1BlockedLiveKdD+0x32fd
[87a52570KHALMNPR.exe]
4c0.0007108a27b6400001208Blockednt!KiFastCallEntry+0xfc
4c0.0007e887a327880001208Blockednt!KiFastCallEntry+0xfc
4c0.00080c8823ada80001208Blockednt!KiFastCallEntry+0xfc
4c0.00081087afe7480001208Blockednt!KiFastCallEntry+0xfc
4c0.0008208823a4300001208Blockednt!KiFastCallEntry+0xfc
4c0.0008d4878efda8ffffffe0Blockednt!KiFastCallEntry+0xfc
4c0.00040087ae2c000001208Blockednt!KiFastCallEntry+0xfc
[8796a3b8wmiprvse.exe]
[87ae4da0MDM.EXE]
90c.000930878eba30fffffffcBlockednt!KiFastCallEntry+0xfc
[8a277370alg.exe]
91c.00095c87adc4e80000603Blockednt!KiFastCallEntry+0xfc
[87a8a020conime.exe]
[8794cbe8dllhost.exe]
f94.000af887a63da8ffffb0d8Blockednt!KiFastCallEntry+0xfc
f94.000eb487a76288ffffafabBlockednt!KiFastCallEntry+0xfc
f94.00089c8788ada8ffffb0aaBlockednt!KiFastCallEntry+0xfc
f94.00090087881020ffffb12aBlockednt!KiFastCallEntry+0xfc
[8794b6b0dllhost.exe]
f5c.000f9c87a379100001208Blockednt!KiFastCallEntry+0xfc
f5c.000a308787a440ffffd6e2Blockednt!KiFastCallEntry+0xfc
f5c.000fe0878c2628ffffb235Blockednt!KiFastCallEntry+0xfc
f5c.000fa4877f62d0ffffb228Blockednt!KiFastCallEntry+0xfc
f5c.000c7487a81928ffffb14fBlockednt!KiFastCallEntry+0xfc
[87893da0msdtc.exe]
[87a959c0firefox.exe]
9bc.000a74876cf718ffffbb31Blockednt!KiFastCallEntry+0xfc
[877a9020plugin-containe]
[8773d258wps.exe]
a10.000dac877bf248ffffaef8Blockednt!KiFastCallEntry+0xfc
a10.00078887479da8ffffb481Blockednt!KiFastCallEntry+0xfc
[877c3020cmd.exe]
[8743da20wmiprvse.exe]
TYPEmismatchforthreadobjectat874a2428
fb4.------NOETHREADDATA
fb4.------NOETHREADDATA
Unabletoread_ETHREADatfe50
[877b05b8livekd.exe]
[87425800kd.exe]
f78.00071887470258ffffaed9RUNNINGLiveKdD+0x32fd
f78.000bd4874a6020fffff013Blockednt!KiFastCallEntry+0xfc
ThreadsProcessed:658
0:kd>
将系统线程映射到一个设备驱动程序上!
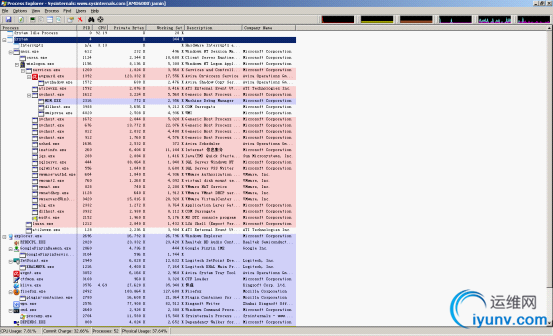
使用PE的system进程上双击,可以看到SRV.SYS有多个线程在运行,按下module可以看到描述
会话管理器windows\system32\smss.EXE是系统中第一个创建的用户模式进程
服务有三种名称:进程名,注册表名,services管理工具的显示名。
Windows的关键组件是什么机制在运行:核心组件机制:对象管理器和同步机制。
|
|
|