|
|
当机器成千上百台增加的时候,如果需要对机器内一台一台的使用密码或者密钥登录,也是一件痛苦的事情,今天分享下使用OpenLDAP实现一个帐号任何机器及应用都可登录。
一.OpenLDAP安装及配置
1.安装依赖包及软件安装
1
| yum install -y openldap openldap-servers openldap-clients openldap-devel
|
2.配置文件配置
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
| cp /usr/share/openldap-servers/slapd.conf.obsolete /etc/openldap/slapd.conf
cp /usr/share/openldap-servers/DB_CONFIG.example /var/lib/ldap/DB_CONFIG
cp /usr/share/doc/sudo-1.8.6p3/schema.OpenLDAP /etc/openldap/schema/sudo.schema
#修改/etc/openldap/slapd.conf文件
找到include /etc/openldap/schema/core.schema在下面增加
include /etc/openldap/schema/sudo.schema
#找到database bdb修改下面的几行
database bdb
suffix "dc=abc,dc=com"
checkpoint 1024 15
rootdn "cn=admin,dc=abc,dc=com"
rootpw admin
loglevel 1
#说明:
database bdb 说明使用Berkeley DB
suffix "dc=abc,dc=com" 域名就是abc.com
checkpoint 1024 15 就是每1M或者每15分钟将缓存刷进磁盘
rootdn "cn=admin,db=abc,dc=com" 管理员是adnin
rootpw admin 管理员的密码就是admin
loglevel 1 日志级别是1
#日志级别
Any (-1, 0xffffffff) //开启所有的dug 信息
Trace (1, 0x1) //跟踪trace 函数调用
Packets (2, 0x2) //与软件包的处理相关的dug 信息
Args (4, 0x4) //全面的debug 信息
Conns (8, 0x8) //链接数管理的相关信息
BER (16, 0x10) //记录包发送和接收的信息
Filter (32, 0x20) //记录过滤处理的过程
Config (64, 0x40) //记录配置文件的相关信息
ACL (128, 0x80) //记录访问控制列表的相关信息
Stats (256, 0x100) //记录链接、操作以及统计信息
Stats2 (512, 0x200) //记录向客户端响应的统计信息
Shell (1024, 0x400) //记录与shell 后端的通信信息
Parse (2048, 0x800) //记录条目的分析结果信息
Sync (16384, 0x4000) //记录数据同步资源消耗的信息
None (32768, 0x8000) //不记录
#在文件最后增加如下,允许用户自行修改密码
access to attrs=shadowLastChange,userPassword
by self write
by * auth
access to *
by * read
|
3.配置OpenLDAP日志
1
2
| echo "local4.* /var/log/sldap.log" >>/etc/rsyslog.conf
/etc/init.d/rsyslog restart
|
4.初始化OpenLDAP
1
2
3
4
5
| service slapd start
rm -rf /etc/openldap/slapd.d/*
slaptest -f /etc/openldap/slapd.conf -F /etc/openldap/slapd.d
chown -R ldap:ldap /etc/openldap/slapd.d/
service slapd restart
|
5.检查服务
1
| netstat -ntlup |grep :389
|
二.迁移用户(将本地的用户和组迁移到OpenLDAP)
1.安装迁移工具
1
2
3
4
5
6
7
8
9
10
| yum install migrationtools -y
cd /usr/share/migrationtools/
[iyunv@kvm242 migrationtools]# ls
migrate_aliases.pl migrate_all_offline.sh migrate_group.pl migrate_profile.pl
migrate_all_netinfo_offline.sh migrate_all_online.sh migrate_hosts.pl migrate_protocols.pl
migrate_all_netinfo_online.sh migrate_automount.pl migrate_netgroup_byhost.pl migrate_rpc.pl
migrate_all_nis_offline.sh migrate_base.pl migrate_netgroup_byuser.pl migrate_services.pl
migrate_all_nis_online.sh migrate_common.ph migrate_netgroup.pl migrate_slapd_conf.pl
migrate_all_nisplus_offline.sh migrate_common.ph.ori migrate_networks.pl
migrate_all_nisplus_online.sh migrate_fstab.pl migrate_passwd.pl
|
2.配置迁移工具,修改migrate_common.ph 71、73行
1
2
3
4
| $DEFAULT_MAIL_DOMAIN = "abc.com";
# Default base
$DEFAULT_BASE = "dc=abc,dc=com";
|
3.导出用户,我这里只导出user1
1
2
3
4
5
6
7
8
9
10
11
12
13
| cd /usr/share/migrationtools/
grep 'user1' /etc/passwd > passwd.in
grep 'user1' /etc/group > group.in
./migrate_base.pl > /tmp/base.ldif
./migrate_passwd.pl passwd.in > /tmp/passwd.ldif
./migrate_group.pl group.in > /tmp/group.ldif
#这里生成了3个OpenLDAP数据
/tmp/base.ldif /tmp/passwd.ldif /tmp/group.ldif
导入数据:
ldapadd -x -D "cn=admin,dc=abc,dc=com" -W -f /tmp/base.ldif
ldapadd -x -D "cn=admin,dc=abc,dc=com" -W -f /tmp/passwd.ldif
ldapadd -x -D "cn=admin,dc=abc,dc=com" -W -f /tmp/group.ldif
|
4.导入sudo基础库
vim /tmp/sudo.ldif
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
| dn: ou=SUDOers,dc=abc,dc=com
objectClass: top
objectClass: organizationalUnit
description: SUDO Configuration Subtree
ou: SUDOers
dn: cn=defaults,ou=SUDOers,dc=abc,dc=com
objectClass: top
objectClass: sudoRole
cn: defaults
description: Default sudoOption's go here
sudoOption: visiblepw
sudoOption: always_set_home
sudoOption: env_reset
dn: cn=root,ou=SUDOers,dc=abc,dc=com
objectClass: top
objectClass: sudoRole
cn: root
sudoUser: root
sudoHost: ALL
sudoRunAsUser: ALL
sudoCommand: ALL
sudoOption: !visiblepw
sudoOption: always_set_home
sudoOption: env_reset
dn: cn=%wheel,ou=SUDOers,dc=abc,dc=com
objectClass: top
objectClass: sudoRole
cn: %wheel
sudoUser: %wheel
sudoHost: ALL
sudoRunAsUser: ALL
sudoCommand: ALL
sudoOption: !authenticate
sudoOption: !visiblepw
sudoOption: always_set_home
sudoOption: env_reset
sudoOption: requiretty
dn: cn=%confops,ou=SUDOers,dc=abc,dc=com
objectClass: top
objectClass: sudoRole
cn: %confops
sudoUser: %confops
sudoHost: ALL
sudoRunAsUser: ALL
sudoOption: !authenticate
sudoOption: !visiblepw
sudoOption: always_set_home
sudoOption: env_reset
sudoCommand: ALL
sudoCommand: !/bin/passwd
dn: cn=%confdev,ou=SUDOers,dc=abc,dc=com
objectClass: top
objectClass: sudoRole
cn: %confdev
sudoUser: %confdev
sudoHost: ALL
sudoRunAsUser: ALL
sudoOption: !authenticate
sudoOption: !visiblepw
sudoOption: always_set_home
sudoOption: env_reset
sudoCommand: /sbin/service
sudoCommand: !/bin/passwd
sudoCommand: /etc/init.d/tomcat
sudoCommand: /bin/kill
sudoCommand: /usr/bin/pkill
sudoCommand: /usr/bin/killall
sudoCommand: /etc/init.d/confservice
sudoCommand: /bin/su - app -s /bin/bash
sudoCommand: /bin/su - tomcat -s /bin/bash
dn: cn=%confqa,ou=SUDOers,dc=abc,dc=com
objectClass: top
objectClass: sudoRole
cn: %confqa
sudoUser: %confqa
sudoHost: ALL
sudoRunAsUser: ALL
sudoOption: !authenticate
sudoOption: !visiblepw
sudoOption: always_set_home
sudoOption: env_reset
sudoCommand: /sbin/service
sudoCommand: !/bin/passwd
sudoCommand: /etc/init.d/confservice
sudoCommand: /bin/kill
sudoCommand: /usr/bin/pkill
sudoCommand: /usr/bin/killall
sudoCommand: /bin/su - app -s /bin/bash
sudoCommand: /bin/su - tomcat -s /bin/bash
sudoCommand: /etc/init.d/tomcat
dn: cn=zabbix,ou=SUDOers,dc=abc,dc=com
objectClass: top
objectClass: sudoRole
cn: zabbix
sudoHost: ALL
sudoUser: zabbix
sudoOption: !authenticate
sudoOption: !visiblepw
sudoOption: always_set_home
sudoOption: env_reset
sudoRunAsUser: root
sudoCommand: !/bin/passwd
sudoCommand: /etc/init.d/tomcat
sudoCommand: /etc/init.d/confservice
sudoCommand: /usr/bin/nmap
sudoCommand: /usr/local/zabbix-ztc/bin/sudo-*
dn: cn=admin,ou=SUDOers,dc=abc,dc=com
objectClass: top
objectClass: sudoRole
cn: admin
sudoHost: ALL
sudoRunAsUser: ALL
sudoOption: !authenticate
sudoOption: !visiblepw
sudoOption: always_set_home
sudoOption: env_reset
sudoCommand: ALL
sudoCommand: !/bin/passwd
sudoUser: admin
|
导入sudo.ldif
1
| ldapadd -x -D "cn=admin,dc=abc,dc=com" -W -f /tmp/sudo.ldif
|
从上面可以看到会生成
SUDOers (OU)
%confdev (cn)
%confops (cn)
%confqa (cn)
%wheel (cn)
admin (cn)
defaults (cn)
root (cn)
zabbix (cn)
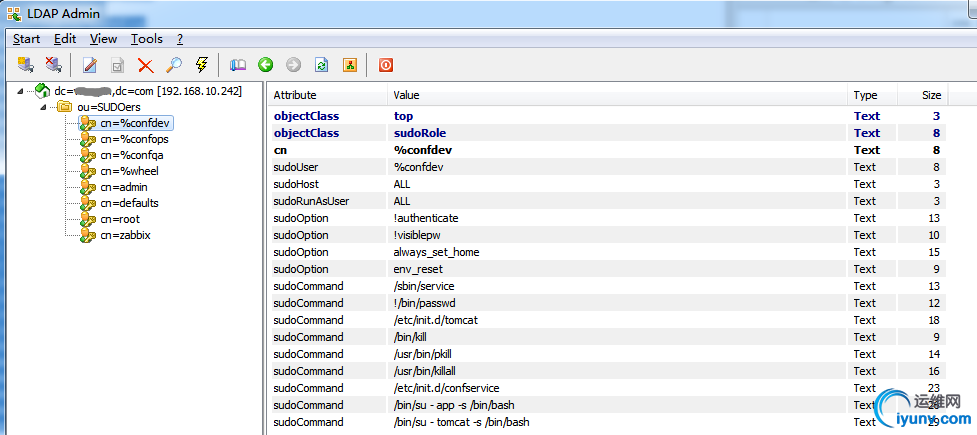
因此只需要建立组confdev,然后将用户拉入confdev组即可有相应的权限,同理zabbix用户也有zabbix相应的权限
二.客户端部署
CentOS 6
1
2
3
4
5
6
| yum -y install openldap openldap-clients nss-pam-ldapd pam_ldap
echo "session required pam_mkhomedir.so skel=/etc/skel umask=0077" >> /etc/pam.d/system-auth
authconfig --savebackup=auth.bak
authconfig --enablemkhomedir --disableldaptls --enableldap --enableldapauth --ldapserver=ldap://192.168.10.242 --ldapbasedn="dc=abc,dc=com" --update
echo -e "uri ldap://192.168.10.242\nSudoers_base ou=SUDOers,dc=abc,dc=com" > /etc/sudo-ldap.conf
echo "Sudoers: files ldap" >> /etc/nsswitch.conf
|
CentOS 5
1
2
3
4
5
6
| yum -y install openldap openldap-clients nss_ldap
echo "session required pam_mkhomedir.so skel=/etc/skel umask=0077" >> /etc/pam.d/system-auth
authconfig --savebackup=auth.bak
authconfig --enableldap --enableldapauth --enablemkhomedir --ldapserver=192.168.10.242 --ldapbasedn="dc=abc,dc=com" --update
echo "Sudoers_base ou=SUDOers,dc=abc,dc=com" >> /etc/ldap.conf
echo "Sudoers: files ldap" >> /etc/nsswitch.conf
|
|
|