一.基本环境:
ldap server: 192.168.8.236 Centos6.5_x86_64
ldap client1: 192.168.8.237 Centos6.5_x86_64
ldap client2: 192.168.8.238 Centos5.4_x86_64
二.安装ldap server:
2.1 安装ldapserver
# yum install -y vim automake autoconf gcc xz ncurses-devel \
patch python-devel git python-pip gcc-c++
# 安装基本环境,后面依赖
# yum install -y openldap openldap-servers openldap-clients openldap-devel
2.2 准备配置文件
# cp /usr/share/openldap-servers/slapd.conf.obsolete /etc/openldap/slapd.conf
## 该文件是slapd的配置文件
# cp /usr/share/openldap-servers/DB_CONFIG.example /var/lib/ldap/DB_CONFIG
## 数据库的配置文件
2.3 修改配置文件# vim /etc/openldap/slapd.conf
...
loglevel 1
...
allow bind_v2
disallow bind_anon
...
TLSCACertificatePath /etc/openldap/cacerts/cacert.pem
TLSCertificateFile /etc/openldap/cacerts/server.cert
TLSCertificateKeyFile /etc/openldap/cacerts/server.key
TLSVerifyClient allow
...
access to *
by dn.exact="uid=jumpserver,ou=People,dc=jumpserver,dc=org" read
by * none
...
suffix "dc=jumpserver,dc=org"
rootdn "cn=admin,dc=jumpserver,dc=org"
rootpw secret234
...
#说明:
loglevel: 设置日志级别 suffix:其实就是BaseDN
disallow: 关闭匿名查询
TLS*: 设置证书文件路径
access: 设置ACL策略,允许uid为jumpserver的cn读取ldap信息
rootdn: 超级管理员的dn
rootpw: 超级管理员的密码
2.4 修改系统日志配置文件
# vim /etc/rsyslog.conf
local4.* /var/log/ldap.log
# local7.*下添加一行
# service rsyslog restart
2.5 建立CA及生成服务端证书
2.5.1 安装openssl
# yum -y install openssl openssl-devel openssl-perl
2.5.2 生成ca证书
# rm -rf /etc/pki/CA/*
# cd /etc/pki/tls/misc
# ./CA.pl -newca
图片:1.png

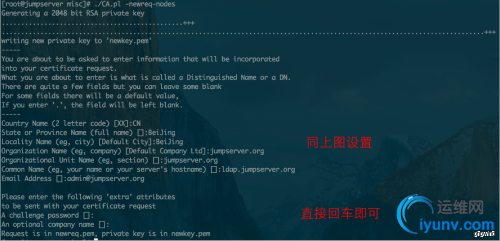
2.5.3 生成ldap server证书
# ./CA.pl -newreq-nodes
图片:2.png
2.5.4 为ldap server证书签名
# ./CA.pl -sign
图片:3.png

2.5.5 更改证书名字,移至配置路径,修改权限
# mv newcert.pem server.cert
# mv newkey.pem server.key
# mkdir /etc/openldap/cacerts
# mv server* /etc/openldap/cacerts/
# cp ../../CA/cacert.pem /etc/openldap/cacerts
# cd /etc/openldap/cacerts
# chown ldap.ldap *
# chmod 644 server.cert
# chmod 600 server.key
2.6 启动slapd, 查看启动情况
# service slapd start
# rm -rf /etc/openldap/slapd.d/*
# slaptest -f /etc/openldap/slapd.conf -F /etc/openldap/slapd.d
# chown -R ldap:ldap /etc/openldap/slapd.d/
# service slapd restart
# netstat -tulnp | grep slapd
#说明:第一次启动生会初始化ldap数据库,在/var/lib/ldap中,如果想删除ldap数据库就删除该目录,保留DB_CONFIG配置文件。新版的ldap使用的是/etc/openldap/slapd.d 下的配置文件,删除原来的配置文件,slaptest是重新生成新的配置文件
2.7 导入ldif数据库框架和测试用户,可以使用migrationtools导出框架,也可以用我导出好的.
# ldapadd -x -W -D "cn=admin,dc=jumpserver,dc=org" -f base.ldif
# ldapadd -x -W -D "cn=admin,dc=jumpserver,dc=org" -f group.ldif
# ldapadd -x -W -D "cn=admin,dc=jumpserver,dc=org" -f passwd.ldif
#说明:测试用户是testuser, 密码是testuser123
acl用户是jumpserver, 密码是jumpserver234
三.安装ldap client:
--- CentOS6设置 ---
2.1 安装LDAP客户端
# yum -y install openldap openldap-clients nss-pam-ldapd pam_ldap
2.2 设置自动创建目录
# echo "session required pam_mkhomedir.so skel=/etc/skel umask=0077" >> /etc/pam.d/system-auth
2.3 把服务器端证书通过scp至客户端:
# scp 192.168.8.237:/etc/openldap/cacerts/cacert.pem /etc/openldap/cacerts/cacert.pem
2.3 备份原来authconfig,然后设置使用LDAP认证
# authconfig --savebackup=auth.bak
# authconfig --enableldap --enableldapauth --enablemkhomedir --enableforcelegacy --enableldaptls --enableldapstarttls --disablesssd --disablesssdauth --ldapserver=ldap.jumpserver.org --ldapbasedn="dc=jumpserver,dc=org" --update
2.4 修改/etc/nslcd.conf:
uid nslcd
gid ldap
uri ldaps://ldap.jumpserver.org/
base dc=jumpserver,dc=org
ssl on
binddn uid=jumpserver,ou=People,dc=jumpserver,dc=org
bindpw jumpserver234
tls_cacertdir /etc/openldap/cacerts
修改/etc/pam_ldap.conf:
base dc=jumpserver,dc=org
uri ldaps://ldap.jumpserver.org
ssl on
binddn uid=jumpserver,ou=People,dc=jumpserver,dc=org
bindpw jumpserver234
tls_cacertdir /etc/openldap/cacerts
pam_password md5
修改/etc/openldap/ldap.conf:
TLS_REQCERT allow
TLS_CACERT /etc/openldap/cacerts/cacert.pem
TLS_CACERTDIR /etc/openldap/cacerts
URI ldaps://ldap.jumpserver.org/
BASE dc=jumpserver,dc=org
修改/etc/sudo-ldap.conf:
uri ldaps://ldap.jumpserver.org
binddn uid=jumpserver,ou=People,dc=jumpserver,dc=org
bindpw jumpserver234
Sudoers_base ou=Sudoers,dc=jumpserver,dc=org
重启nslcd服务 /etc/init.d/nslcd restart
添加开机启动 chkconfig nslcd on
--- CentOS5设置 ---
2.1 安装LDAP客户端
# yum -y install openldap openldap-clients nss_ldap
2.2 设置自动创建目录
# echo "session required pam_mkhomedir.so skel=/etc/skel umask=0077" >> /etc/pam.d/system-auth
# scp cacert.pem 192.168.8.237:/tmp/
2.3 把服务器端证书通过scp传至客户端:
# scp 192.168.8.237:/etc/openldap/cacerts/cacert.pem /etc/openldap/cacerts/cacert.pem
2.3 设置使用LDAP认证
# authconfig --enableldap --enableldapauth --enablemkhomedir --ldapserver=ldap.jumpserver.org --ldapbasedn="dc=jumpserver,dc=org" --update
2.4 修改/etc/ldap.conf:
base dc=jumpserver,dc=org
timelimit 120
bind_timelimit 120
idle_timelimit 3600
nss_initgroups_ignoreusers root,ldap,named,avahi,haldaemon,dbus,radvd,tomcat,radiusd,news,mailman,nscd,gdm,mysql,nagios,zabbix,admin
uri ldaps://ldap.jumpserver.org/
ssl on
binddn uid=jumpserver,ou=People,dc=jumpserver,dc=org
bindpw jumpserver234
tls_cacertdir /etc/openldap/cacerts
pam_password md5
Sudoers_base ou=Sudoers,dc=jumpserver,dc=org
修改/etc/openldap/ldap.conf:
TLS_REQCERT allow
TLS_CACERT /etc/openldap/cacerts/cacert.pem
TLS_CACERTDIR /etc/openldap/cacerts
URI ldaps://ldap.jumpserver.org/
BASE dc=jumpserver,dc=org
重启nscd服务 /etc/init.d/nscd restart
添加开机启动 chkconfig nscd on
2.4 从jumpserver连接testuser测试
# 密码是testuser123 如果连接成功则证明OK.