|
|
前言 软件负载均衡一般通过两种方式来实现:基于操作系统的软负载实现和基于第三方应用的软负载均衡。LVS是基于Linux操作系统实现的一种软负载,而Haproxy则是基于第三方应用实现的软负载。Haproxy相比LVS的使用要简单很多,但跟LVS一样,Haproxy自己并不能实现高可用,一旦Haprox节点故障,将会影响整个站点。本文是haprox基于keepalived实现web高可用及动静分离。
相关介绍
HAProxy
haproxy是一款提供高可用性、负载均衡以及基于TCP和HTTP应用的代理软件,Haproxy是完全免费的,借助Haproxy可以快速并且可靠的提供基于TCP和HTTP应用的代理解决方案。Haproxy适用于那些负载较大的Web站点,这些站点通常又需要会话保持或七层出来。Haproxy可以支持数以万计的并发连接,并且Haproxy的运行模式使得它可以很简单安全的整合进架构中,同时可以包含web服务器不被暴露在网络上。
keepalived
keepalived是基于VRRP(virtual router redundancy protocol,虚拟路由冗余协议)热备份协议工作的,以软件的方式实现linux服务器的多机热备功能。VRRP是针对路由器的一种备份解决方案----由多台路由器组成一个热备组。通过共用的虚拟IP地址对外提供服务;每个热备组内同一时刻只有一台主服务器提供服务,其他服务器处于冗余状态,若当前在线的服务器失败,其他服务器会自动接替(优先级决定接替顺序)虚拟IP地址,以继续提供服务。
高可用解决方案拓扑
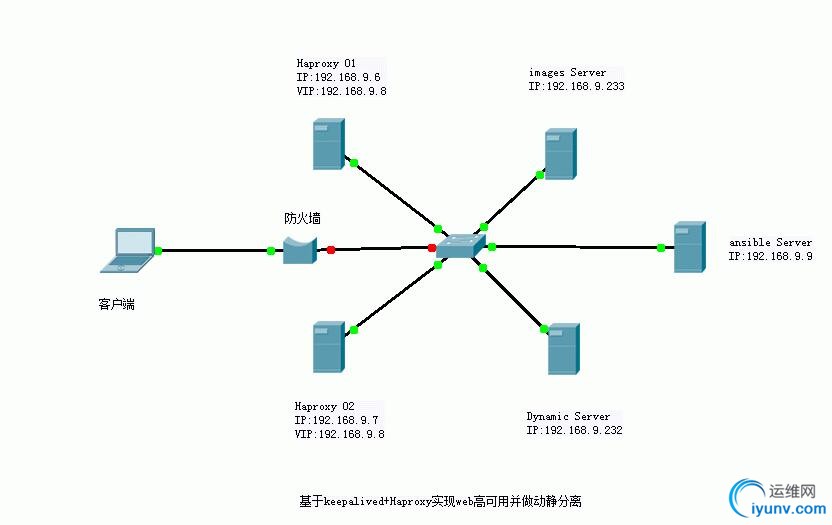
一、测试环境:Centos6.5;使用5台虚拟机
1
2
3
4
5
6
7
| 分别对他们设置主机名:
主机名 ip地址 软件包
mail 192.168.9.9 ansible
node1 192.168.9.6 haproxy+keepalived
node2 192.168.9.7 haproxy+keepalived
node3 192.168.9.233 httpd
node4 192.168.9.232 LAMP
|
二、准备工作:这里基于ansible做一下简单部署
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
| 1、基于ssh通信,先做密钥;
# ssh-copy-id -i /root/.ssh/id_rsa.pub node1
# ssh-copy-id -i /root/.ssh/id_rsa.pub node2
# ssh-copy-id -i /root/.ssh/id_rsa.pub node3
# ssh-copy-id -i /root/.ssh/id_rsa.pub node4
2、ansible设置及管理节点探测:
# cd /etc/ansible/
# vim hosts
[haproxy]
node1
node2
[images]
node3
[dynamic]
node4
# ansible all -m ping
node3 | success >> {
"changed": false,
"ping": "pong"
}
node1 | success >> {
"changed": false,
"ping": "pong"
}
node2 | success >> {
"changed": false,
"ping": "pong"
}
node4 | success >> {
"changed": false,
"ping": "pong"
}
|
三、在node1和node2上安装haproxy和keepalived
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
| 时间同步
# ansible haproxy -m shell -a 'ntpdate cn.pool.ntp.org'
node1 | success | rc=0 >>
21 Jan 16:34:32 ntpdate[3481]: step time server 202.112.29.82 offset -2.284555 sec
node2 | success | rc=0 >>
21 Jan 16:34:47 ntpdate[3286]: step time server 202.112.29.82 offset -2.287749 sec
# ansible haproxy -m shell -a 'date'
node1 | success | rc=0 >>
Thu Jan 21 16:43:37 HKT 2016
node2 | success | rc=0 >>
Thu Jan 21 16:43:37 HKT 2016
主机互信
[iyunv@node1 ~]# ssh-keygen -t rsa
[iyunv@node1 ~]# ssh-copy-id -i /root/.ssh/id_rsa.pub node2
[iyunv@node2 ~]# ssh-keygen -t rsa
[iyunv@node2 ~]# ssh-copy-id -i /root/.ssh/id_rsa.pub node1
安装所需程序
# ansible haproxy -m shell -a 'yum -y install haproxy keepalived'
1、配置keepalived
在node1节点上修改keepalived
[iyunv@node1 keepalived]# cp keepalived.conf{,.bak}
[iyunv@node1 keepalived]# ls
keepalived.conf keepalived.conf.bak
[iyunv@node1 keepalived]# vim keepalived.conf
vrrp_instance VI_1 { #定义VRRP实例,实例名自定义
state MASTER #指定keepalived的角色,MASTER为主服务器,BACKUP为备用服务器
interface eth0 #指定HA监测的接口
virtual_router_id 61 #虚拟路由标识(1-255),在一个VRRP实例中主备服务器ID必须一样
priority 100 #优先级,数字越大优先级越高,主必须大于备
advert_int 1 #设置主备之间同步检查时间间隔,单位秒
authentication { #设置验证类型和密码
auth_type PASS #验证类型
auth_pass 12345678 #设置验证密码,同一实例中主备密码
}
virtual_ipaddress {
192.168.9.8
}
[iyunv@node1 keepalived]# scp keepalived.conf node2:/etc/keepalived
keepalived.conf 100% 515 0.5KB/s 00:00
在node2节点上修改keepalived
vrrp_instance VI_1 {
state BACKUP
interface eth0
virtual_router_id 61
priority 98
advert_int 1
authentication {
auth_type PASS
auth_pass 12345678
}
virtual_ipaddress {
192.168.9.8
}
# ansible haproxy -m shell -a 'service keepalived start'
node1 | success | rc=0 >>
Starting keepalived: [ OK ]
node2 | success | rc=0 >>
Starting keepalived: [ OK ]
# ansible haproxy -m shell -a 'ip addr show'
node2 | success | rc=0 >>
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 16436 qdisc noqueue state UNKNOWN
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
link/ether 00:0c:29:a3:a6:aa brd ff:ff:ff:ff:ff:ff
inet 192.168.9.7/22 brd 192.168.11.255 scope global eth0
inet6 fe80::20c:29ff:fea3:a6aa/64 scope link
valid_lft forever preferred_lft forever
node1 | success | rc=0 >>
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 16436 qdisc noqueue state UNKNOWN
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
link/ether 00:0c:29:20:16:2e brd ff:ff:ff:ff:ff:ff
inet 192.168.9.6/22 brd 192.168.11.255 scope global eth0
inet 192.168.9.8/32 scope global eth0
inet6 fe80::20c:29ff:fe20:162e/64 scope link
valid_lft forever preferred_lft forever
###可以看出VIP在node1上
2、配置Haproxy
|
|
|
|