1.课程目标
- 了解RedhatLinux中的HTTP Server----Apache;
- 掌握Apache服务的安装、启动、开机自动加载;
- 掌握Apache的基本配置:默认站点、个人主页;
- 掌握Apache的高级配置:虚拟主机、用户访问控制、用户验证登录、TLS网站加密、动态Web;
- 掌握Apache的Options选项:Indexes、FollowSymlinks。
2.Web服务器概述
2.1.Web简介
Web服务器也成为WWW服务器,主要提供网上信息浏览服务。WWW是Internet的多媒体信息查询工具,正是因为有了WWW工具,才使得Internet迅速发展。
WWW(World Wide Web,环球信息网),简称Web,一般叫“万维网”。通过“万维网”,用简单的方法,就可以获取丰富的信息资料。且界面友好。
WWW采用C/S结构,作用就是整理和存储各种资源,并响应客户端软件请求,把客户端所需要的资源下载下来
2.2.HTTP&HTTPS协议简介
- HTTP(HyperText Transfer Protocol,超文本传输协议)
HTTP是Internet上应用最广泛的网络协议,WWW都遵循这个标准。它是一个C/S请求和应答的标准,使用TCP传输协议,保证数据传输的正确、有序。
通过web浏览器,HTTP客户端使用URL(Uniform/UniversalResource Locator,同一资源定位符)发起一个请求,建立一个到服务器web端口(缺省80端口)的TCP连接。HTTP服务器在这个指定端口侦听客户端发送来的请求。收到请求后,向客户端发送状态码和响应消息(消息体可能是文件、错误消息、其他信息)。
- HTTPS(Hypertext Transfer Protocol Over Secure Socket Layer,基于SSL的HTTP协议)
HTTPS虽然使用了HTTP协议,但是又不同于HTTP协议。它提供了身份验证与加密通信方法,被广泛用于互联网上安全敏感的通信。在访问HTTPS网站时,URL不再是以http开头,而是以https开头。视同HTTPS时,客户端与服务器的通信过程如下: - 客户使用https地址访问Web服务器,要求与Web服务器建立SSL连接;
- Web服务器收到客户端请求后,将网站的证书信息(证书中包含公钥)传送给客户端;
- 客户端的浏览器与Web服务器开始协商SSL连接的安全等级,即信息加密等级;
- 客户端的浏览器根据双方同意的安全等级,建立会话密钥,然后用Web服务器端的公钥将会话密钥加密,并传送给服务器;
- Web服务器利用自己的私钥解密出会话密钥;
- Web服务器利用会话密钥加密与客户端之间的通信。
3.Apache简介
Web服务软件非常多,常见的由Apache、Nginx、Lighttpd、微软的IIS(Internet Information Services,互联网信息服务)。但是当今市面上用的最多的当属Apache(稳定)。
Apache HTTP Server是Apache软件基金会的一个开源Web服务器,可以在大多数操作系统中运行,由于其多平台、安全性、稳定性而被广泛使用,是最流行的Web服务器软件。
Apache支持许多特性,这些特性大部分通过编译的模块实现。这些特性包括:服务端的编程语言支持、身份认证方案以及目前最流行的Web服务器应用。由于Apache的开放性,目前也有很多非官方的模块用以满足某些特殊的应用。
Apache凭借其良好的稳定性、安全性以及多平台应用而被广泛的使用,本部分实验,我们就来介绍Redhat Linux7上的Apache配置,更好的了解RHEL7上Apache的新特性。
注:
4.Apache相关配置
4.1.Apache安装及启动
RHEL7上默认没有安装Apache HttpServer,需要我们自行安装。如下:
[iyunv@server30 ~]# yum -y install http*
Loaded plugins: langpacks, product-id, subscription-manager
This system is not registered to Red Hat Subscription Management. You can use subscription-manager to register.
base | 4.1 kB 00:00
Resolving Dependencies
……………
|
注:
- 安装时加“*”,不仅安装正常的服务及程序,同时安装其他一些需要的内容,如:服务用的模板,方便我们后面实验所需。
启动服务
[iyunv@server30 ~]# systemctl restart httpd
[iyunv@server30 ~]# systemctl enable httpd
ln -s '/usr/lib/systemd/system/httpd.service' '/etc/systemd/system/multi-user.target.wants/httpd.service'
[iyunv@server30 ~]# systemctl status httpd
httpd.service - The Apache HTTP Server
Loaded: loaded (/usr/lib/systemd/system/httpd.service; enabled)
Active: active (running) since Tue 2015-05-19 18:00:39 CST; 12s ago
Main PID: 5896 (httpd)
Status: "Total requests: 0; Current requests/sec: 0; Current traffic: 0 B/sec"
CGroup: /system.slice/httpd.service
├─5896 /usr/sbin/httpd -DFOREGROUND
├─5897 /usr/sbin/httpd -DFOREGROUND
├─5898 /usr/sbin/httpd -DFOREGROUND
├─5899 /usr/sbin/httpd -DFOREGROUND
├─5900 /usr/sbin/httpd -DFOREGROUND
└─5901 /usr/sbin/httpd -DFOREGROUND
May 19 18:00:39 server30.example.com systemd[1]: Starting The Apache HTTP Se....
May 19 18:00:39 server30.example.com systemd[1]: Started The Apache HTTP Server.
Hint: Some lines were ellipsized, use -l to show in full.
|
4.2.Apache主配置文件
Redhat Linux7(RHEL7)与RHEL6一样,主配置文件都在/etc/httpd/conf/httpd.conf,但是又有所不同。
查看主配置文件行数
[iyunv@server30 httpd]# wc -l conf/httpd.conf
353 conf/httpd.conf
|
一共353行。而我们知道,在RHEL6中,Apache安装好之后,主配置文件是有1000多行的,区别在哪里呢?
RHEL6中,Apache安装过程中,把所有web服务使用的模块都安装了,这是所谓的“重量级安装”。而RHEL7就是“轻量级”安装,只安装缺省的服务,模块没有安装,要使用什么模块自行安装使用,以此对服务进行初始的简化。
打开主配置文件
[iyunv@server30 httpd]# vim /etc/httpd/conf/httpd.conf
………前面省略部分…………..
# Load config files in the "/etc/httpd/conf.d" directory, if any.
IncludeOptional conf.d/*.conf
|
查看主配置文件最后一行,如上:内容显示加载的配置文件在/etc/httpd/conf.d下,以.conf结尾。
[iyunv@server30 httpd]# ll /etc/httpd/conf.d/
total 24
-rw-r--r--. 1 root root 2893 Mar 20 2014 autoindex.conf
-rw-r--r--. 1 root root 1511 May 19 19:29 httpd-vhosts.conf
-rw-r--r--. 1 root root 295 Mar 20 2014 manual.conf
-rw-r--r--. 1 root root 366 Mar 20 2014 README
-rw-r--r--. 1 root root 1252 Mar 20 2014 userdir.conf
//个人主页文件
-rw-r--r--. 1 root root 516 Mar 20 2014 welcome.conf
|
4.3.Web与DNS的关系
我们知道,访问网页是通过URL即 http://www.baidu.com的方式实现的,通过域名来解析IP地址,实现网页的访问,而这个过程是需要DNS(Domain Name Server)来实现的。否则,我们访问网页只能通过IP的形式来实现,对于专业人士来说,可能不算什么,但是对于非专业人士来说,通过IP访问网页就是件很难的事了。所以,本部分内容我们主要介绍怎样通过DNS来实现域名解析IP,实现网页访问。
DNS的安装,启动及配主配置文件的设置详见【第四章:DNS】,本部分主要介绍如何配置解析文件来实现域名的解析。
假设现在服务器端server30.example.com(172.16.30.130)有网站server30.example.com(IP:172.16.30.130),www.example.com(IP:172.16.30.130),那么怎样实现解析呢?如下:
[iyunv@server30 ~]# vim /etc/unbound/local.d/example.conf
local-zone: "example.com." static
local-data: "example.com. IN SOA ns.example.com. root 1 1D 1H 1W 1H"
local-data: "ns.example.com. IN A 172.16.30.130"
local-data: "server30.example.com. IN A 172.16.30.130"
local-data: "www.example.com. IN A 172.16.30.130"
local-data-ptr: "172.16.30.130 ns.example.com."
local-data-ptr: "172.16.30.130 server30.example.com."
local-data-ptr: "172.16.30.130 www.example.com."
|
配置完解析文件,可以使用unbound-check检查配置,然后重启服务
[iyunv@freeit ~]# unbound-checkconf
unbound-checkconf: no errors in /etc/unbound/unbound.conf
[iyunv@freeit ~]# systemctl restart unbound
|
服务器端配置完DNS之后,就可以在客户端指定DNS Server并进行验证
[iyunv@desktop30 ~]# vim /etc/resolv.conf
# Generated by NetworkManager
search example.com
nameserver 172.16.30.130
[iyunv@desktop30 ~]# nslookup
> server30.example.com
Server: 172.16.30.130
Address: 172.16.30.130#53
Name: server30.example.com
Address: 172.16.30.130
> www.example.com
Server: 172.16.30.130
Address: 172.16.30.130#53
Name: www.example.com
Address: 172.16.30.130
|
解析成功,之后就可以在服务器端配置Web服务并通过域名访问。
4.4.基本网页实现
Apache安装之后,其默认的DocumentRoot为/var/www/html。安装并启动服务之后,我们就可以通过简单的配置来实现基本的网页访问,缺省我们使用DNS解析中的server30.example.com作为Wen的网页地址。配置如下:
在DocumentRoot创建站点的索引文件
[iyunv@server30 ~]# cd /var/www/html/
[iyunv@server30 html]# vim index.html
Hello! server30.example.com
//网站访问成功后显示的内容呢
~
|
重启服务
[iyunv@server30 html]# systemctl restart httpd.service
|
我们知道,Redhat Linux7中使用的防火墙为Firewall,缺省值允许SSH&dhcpv6-client。其它服务均拒绝,所以,要实现访问,必须设置防火墙允许http,可以使用RichRules,可以针对具体的Server。本实验针对具体server开启防火墙
[iyunv@server30 html]# firewall-cmd --add-service=http --permanent
success
[iyunv@server30 html]# firewall-cmd --reload
success
[iyunv@server30 html]# firewall-cmd --list-all
public (default, active)
interfaces: eno16777736
sources:
services: dhcpv6-client http nfs rpc-bind ssh
ports:
masquerade: no
forward-ports:
icmp-blocks:
rich rules:
|
客户端访问网页测试
①此处填写web服务器的地址
4.5.个人主页
涉及到个人主页,那么我们就要去到/etc/httpd/conf.d/userdir.conf,去配置此文件。首先打开查看此文件
[iyunv@server30 httpd]# vim /etc/httpd/conf.d/userdir.conf
1 #
2 # UserDir: The name of the directory that is appended onto a user's home
3 # directory if a ~user request is received.
4 #
5 # The path to the end user account 'public_html' directory must be
6 # accessible to the webserver userid. This usually means that ~userid
7 # must have permissions of 711, ~userid/public_html must have permissions
8 # of 755, and documents contained therein must be world-readable.
9 # Otherwise, the client will only receive a "403 Forbidden" message.
10 #
11 <IfModule mod_userdir.c>
12 #
13 # UserDir is disabled by default since it can confirm the presence
14 # of a username on the system (depending on home directory
15 # permissions).
16 #
17 UserDir disabled
18
19 #
20 # To enable requests to /~user/ to serve the user's public_html
21 # directory, remove the "UserDir disabled" line above, and uncomment
22 # the following line instead:
23 #
24 #UserDir public_html
25 </IfModule>
26
27 #
28 # Control access to UserDir directories. The following is an example
29 # for a site where these directories are restricted to read-only.
30 #
31 <Directory "/home/*/public_html">
32 AllowOverride FileInfo AuthConfig Limit Indexes
33 Options MultiViews Indexes SymLinksIfOwnerMatch IncludesNoExec
34 Require method GET POST OPTIONS
35 </Directory>
36
|
如上:只有36行,第17行为个人主页的开关。缺省关闭。既然要设计个人主页,那么就要打开此开关。第24行为个人主页的目录,为注释行,同样要去掉注释,打开此功能
17 #UserDir disabled
18 UserDir enabled
25 #UserDir public_html
26 UserDir public_html
|
对于配置文件,一般建议不要直接修改模板,所以此处注释掉第17行,另复制一行,改disabled为enabled;复制#UserDir public_html并另起一行粘贴,去掉注释。
以用户user1为例,创建个人主页的主目录并在目录下创建索引文件
[iyunv@server30 ~]# id user1
uid=1001(user1) gid=1001(user1) groups=1001(user1)
[iyunv@server30 ~]# mkdir /home/user1/public_html
[iyunv@server30 ~]# vim /home/user1/public_html/index.html
Hello! My name is user1!
Let's make friends !
//索引文件内容
|
根据配置文件提示,用户的家目录要有755的权限才能访问成功,/home/user1及/home/user1/public_html都要有755的权限,后者默认为755,所以只需给前者设置755权限即可
[iyunv@server30 ~]# chmod 755 /home/user1/
[iyunv@server30 ~]# ll /home/
total 0
drwxr-xr-x. 4 user1 user1 92 May 19 20:19 user1
[iyunv@server30 ~]# ll /home/user1/
total 0
drwxr-xr-x. 2 root root 23 May 19 20:20 public_html
|
开启httpd个人主页的bool开关
[iyunv@server30 ~]# systemctl restart httpd.service
[iyunv@server30 ~]# getsebool -a |grep httpd |grep home
httpd_enable_homedirs --> off
[iyunv@server30 ~]# setsebool -P httpd_enable_homedirs on
|
重启服务,客户端访问验证
[iyunv@server30 ~]# systemctl restart httpd.service
|
根据个人主页原始配置文件第20行的提示,访问个人主页要在URL后加上/~user
①访问URL后要加/~user1
如上,/~user1这样的方式是不是很不友好,那么我们就采用一种方法去掉这个“~”符号,如下:
[iyunv@server30 ~]# ln -s /home/user1/public_html/index.html /var/www/html/user1
[iyunv@server30 public_html]# ll /var/www/html/
total 4
-rw-r--r--. 1 root root 28 May 19 18:29 index.html
lrwxrwxrwx. 1 root root 34 May 19 20:58 user1 -> /home/user1/public_html/index.html
[iyunv@server30 ~]# systemctl restart httpd.service
|
如上:做一个链接到/var/www/html,然后再次访问,去掉“~”。
①URL不再需要加“~”符号
这样的访问方式就友好多了。
4.6.虚拟主机
虚拟主机是服务器采用的节省服务器硬件成本的技术,把两个或多个网站配置在同一台主机上来实现。经一台服务器的某项或者全部服务内容逻辑划分为多个服务单位,对外表现为多个服务器,从而充分利用服务器硬件资源。
由于多台虚拟服务器共享一台真实服务器的资源,每个用户承受的硬件费用、网络维护费用、通信线路的费用均大幅度降低。如今,几乎所有的公司都在网络上建立了自己的web服务器,其中有相当的部分采用的是虚拟主机。
现在假设在server30.example.com这台主机上要设置两个web服务:http://server30.example.com,http://www.example.com,前者DocumentRoot路径为:/var/www/html,后者DocumentRoot路径为: /var/www/virtual.请通过虚拟主机实现设置。
虚拟主机的要用到配置文件,而/etc/httpd/conf/httpd.conf是没有虚拟主机设置选项的。需要我们使用安装的模板文件(这也是为什么安装http服务时要加上“*”),调用到/etc/httpd/conf.d下,如下:
[iyunv@server30 ~]# cd /etc/httpd/conf.d/
[iyunv@server30 conf.d]# cp -p /usr/share/doc/httpd-2.4.6/httpd-vhosts.conf .
cp: overwrite ‘./httpd-vhosts.conf’? y
[iyunv@server30 conf.d]# ll
total 24
-rw-r--r--. 1 root root 2893 Mar 20 2014 autoindex.conf
-rw-r--r--. 1 root root 1511 Mar 20 2014 httpd-vhosts.conf
-rw-r--r--. 1 root root 295 Mar 20 2014 manual.conf
-rw-r--r--. 1 root root 366 Mar 20 2014 README
-rw-r--r--. 1 root root 1297 May 19 20:37 userdir.conf
-rw-r--r--. 1 root root 516 Mar 20 2014 welcome.conf
|
打开文件查看
[iyunv@server30 conf.d]# vim httpd-vhosts.conf
5 # If you want to maintain multiple domains/hostnames on your
6 # machine you can setup VirtualHost containers for them. Most configurations
7 # use only name-based virtual hosts so the server doesn't need to worry abou
t
8 # IP addresses. This is indicated by the asterisks in the directives below.
9 #
10 # Please see the documentation at
11 # <URL:http://httpd.apache.org/docs/2.4/vhosts/>
12 # for further details before you try to setup virtual hosts.
13 #
14 # You may use the command line option '-S' to verify your virtual host
15 # configuration.
16
17 #
18 # VirtualHost example:
19 # Almost any Apache directive may go into a VirtualHost container.
20 # The first VirtualHost section is used for all requests that do not
21 # match a ServerName or ServerAlias in any <VirtualHost> block.
22 #
23 <VirtualHost *:@@Port@@>
24 ServerAdmin webmaster@dummy-host.example.com
25 DocumentRoot "@@ServerRoot@@/docs/dummy-host.example.com"
26 ServerName dummy-host.example.com
27 ServerAlias www.dummy-host.example.com
28 ErrorLog "/var/log/httpd/dummy-host.example.com-error_log"
29 CustomLog "/var/log/httpd/dummy-host.example.com-access_log" common
30 </VirtualHost>
31
32 <VirtualHost *:@@Port@@>
33 ServerAdmin webmaster@dummy-host2.example.com
34 DocumentRoot "@@ServerRoot@@/docs/dummy-host2.example.com"
35 ServerName dummy-host2.example.com
36 ErrorLog "/var/log/httpd/dummy-host2.example.com-error_log"
37 CustomLog "/var/log/httpd/dummy-host2.example.com-access_log" common
38 </VirtualHost>
|
有效行为38行,我们可以复制23到28行内容设置虚拟主机,复制后直接进行修改,如下,为修改后的内容
40 <VirtualHost 172.16.30.130:80> ①
41 ServerAdmin root@server30.example.com ②
42 DocumentRoot "/var/www/html" ③
43 ServerName server30.example.com ④
44 ErrorLog "/var/log/httpd/server30.example.com-error_log" ⑤
45 CustomLog "/var/log/httpd/server30.example.com-access_log" common ⑥
46 </VirtualHost>
47
48 <VirtualHost 172.16.30.130:80>
49 ServerAdmin root@www.example.com
50 DocumentRoot "/var/www/virtual"
51 ServerName www.example.com
52 ErrorLog "/var/log/httpd/www.example.com-error_log"
53 CustomLog "/var/log/httpd/www.example.com-access_log" common
54 </VirtualHost>
|
各行含义如下
①指定172.16.30.130的80端口建立该虚拟主机
②指定该虚拟主机管理员邮箱,非必须参数
③指定使用172.16.30.130的IP地址访问时网站内容的存放目录
④帮主Apache识别该虚拟主机FQDN(如果此处为IP,就是帮助识别虚拟主机的IP地址及端口为【IP:portnumber】),非必须参数
⑤指定使用server30.example.com访问时网站错误日志的存放地点,非必须参数
⑥指定使用server30.example.com访问时网站访问日志的存放地点,非必须参数
默认的server30.example.com的站点前面已经创建过索引文件,所以,只需创建另一个虚拟主机的主目录及索引文件即可:
[iyunv@server30 conf.d]# mkdir /var/www/virtual
[iyunv@server30 conf.d]# vim /var/www/virtual/index.html
Hello! www.example.com
~
//索引文件内容
|
重启服务,客户端访问验证
[iyunv@server30 ~]# systemctl restart httpd.service
|
客户端访问验证
访问成功,虚拟主机配置完成。
4.7. <Directory>的Options选项
Apache服务的主配置文件中<Directory>有两个options选项,一个为Indexes,另一个为FollowSymlinks。需要添加<Directory></Directory>。
是否列出该文件下的内容,若文件下有index.html文件,不管怎么设置,都会显示index.html下的内容。如果没有index.html文件,则当有indexes这个参数时,就显示该文件下的内容,没有Indexes参数时,显示网页无法显示。
是否显示目录下的链接文件。此参数的使用是在没有Index.html文件但有indexes参数时。此参数起作用的前提是有Indexes参数的存在。
注:
- 两个参数默认是打开的,若手动建立了站点需要手动打开;
- Indexes和FollowSymlinks参数对应的只是虚拟目录。Indexes所对应的目录应该是<Directory /var/www/html/data>的data目录。FollowSymlinks对应的邻接文件也是说的data下的连接文件。
在/var/www/html/下创建data目录,并复制/etc/passwd到此目录做验证用,把/etc链接到此目录下,命名为test,为后续试验做准备
[iyunv@server30 conf.d]# mkdir /var/www/html/data
[iyunv@server30 conf.d]# cd /var/www/html/data
[iyunv@server30 data]# cp /etc/passwd .
[iyunv@server30 data]# ln -s /etc test
[iyunv@server30 data]#
[iyunv@server30 data]# ll
total 4
-rw-r--r--. 1 root root 2011 May 19 23:35 passwd
lrwxrwxrwx. 1 root root 11 May 19 23:36 test -> /etc/shadow
|
在/var/www/html/data下创建一个索引文件
[iyunv@server30 data]# vim index.html
hello! this is /var/www/html/data
~
|
虚拟主机配置文件设置
40 <VirtualHost 172.16.30.130:80>
41 ServerAdmin root@server30.example.com
42 DocumentRoot "/var/www/html"
43 <Directory /var/www/html/data>
44 </Directory>
45 ServerName server30.example.com
46 ErrorLog "/var/log/httpd/server30.example.com-error_log"
47 CustomLog "/var/log/httpd/server30.example.com-access_log" common
48 </VirtualHost>
|
重启服务
[iyunv@server30 data]# systemctl restart httpd.service
|
客户端访问验证
访问成功。
4.7.1.Indexes参数
下面,删除索引文件,加上Options选项的FollowSymLinks重启服务再次查看
[iyunv@server30 data]# rm -rf index.html
[iyunv@server30 data]# ls
1 passwd test
-----------------------添加options选项-----------------------
40 <VirtualHost 172.16.30.130:80>
41 ServerAdmin root@server30.example.com
42 DocumentRoot "/var/www/html"
43 <Directory /var/www/html/data>
44 options FollowSymLinks
45 </Directory>
46 ServerName server30.example.com
47 ErrorLog "/var/log/httpd/server30.example.com-error_log"
48 CustomLog "/var/log/httpd/server30.example.com-access_log" common
49 </VirtualHost>
---------------重启服务---------------------
[iyunv@server30 data]# systemctl restart httpd.service
|
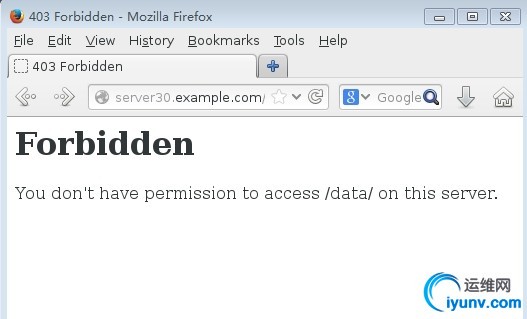
如上,删除索引文件之后,只加FollowSymLinks参数是不能访问网页的,没有索引文件的前提是要有indexes参数。
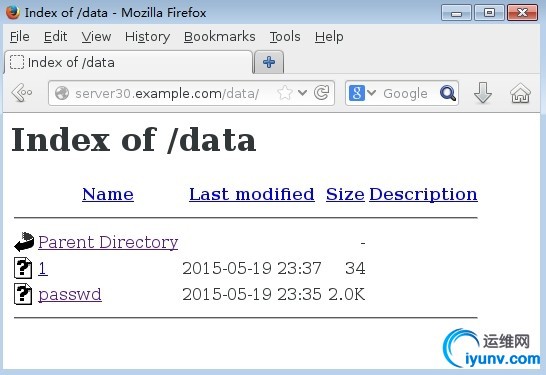
加上indexes参数再次查看
----------------------------------------添加options选项的indexes参数----------------------
40 <VirtualHost 172.16.30.130:80>
41 ServerAdmin root@server30.example.com
42 DocumentRoot "/var/www/html"
43 <Directory /var/www/html/data>
44 options Indexes FollowSymLinks
45 </Directory>
46 ServerName server30.example.com
47 ErrorLog "/var/log/httpd/server30.example.com-error_log"
48 CustomLog "/var/log/httpd/server30.example.com-access_log" common
49 </VirtualHost>
-------------------重启服务-----------------------------
[iyunv@server30 data]# systemctl restart httpd.service
|
客户端访问验证
可以看到所有,包括链接文件。
4.7.2.FollowSymLinks参数
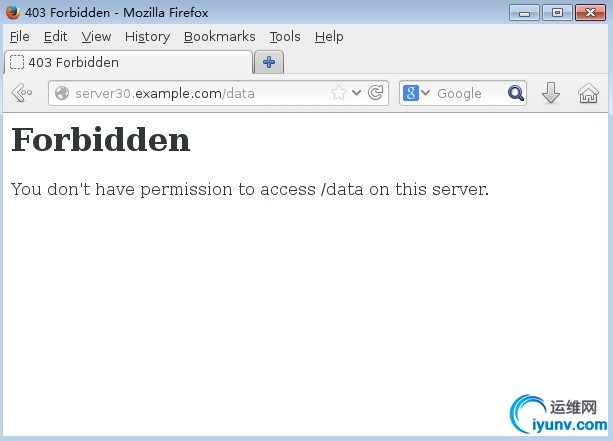
接下来去掉FollowSymLinks参数再次查看
-----------------去掉options选项的FollowSymLinks参数-----------
40 <VirtualHost 172.16.30.130:80>
41 ServerAdmin root@server30.example.com
42 DocumentRoot "/var/www/html"
43 <Directory /var/www/html/data>
44 options Indexes
45 </Directory>
46 ServerName server30.example.com
47 ErrorLog "/var/log/httpd/server30.example.com-error_log"
48 CustomLog "/var/log/httpd/server30.example.com-access_log" common
49 </VirtualHost>
-------------------------重启服务----------------------
[iyunv@server30 data]# systemctl restart httpd.service
|
客户端查看验证
如上,去掉此参数后,链接文件就访问不到了。
4.8.访问控制
在Firewall的章节中,我们介绍过数据包到达Linux后的一个过滤规则,首先是由Firewall进行过滤,然后经由TCP_Wrappers过滤,再有服务本身进行过滤,最后经过最严格的SELinnux进行过滤。防火墙的过滤规则已经够详细,够严格,暂且不说。而对于TCP_Wrappers,并不是针对所有服务有效,它只对具有libwrap.so动态连接库的服务生效。HTTP服务是没有此组件的,所以不能通过TCP_Wrappers进行过滤。在friewall放行http请求的情况下,要进行数据包的过滤,只能通过服务本身来进行严格的限制,那么要怎样通过HTTP服务本身进行限制呢?下面我们将详细介绍下如何在Apache下通过服务本身进行数据包的过滤。
Redhat Linux7中有的Apache有两种过滤方式:order参数和Require。下面我们针对两种方法来进行简单的介绍。
4.8.1.Order参数
Apache的自身过滤规则需要在配置文件中添加参数:order,后跟deny、allow。 Order后的allow和deny顺序为
- 若allow在前,deny在后,则是先允许再拒绝,当允许与拒绝发生冲突时,拒绝优先;
- 多deny在前,allow在后,则是先拒绝再允许,当拒绝与允许发生冲突时,允许优先;
- 两者遵循规则为:冲突时,谁在后谁优先。
注:
- Order参数如果添加在<Directory></Directory>之间,则是对<Directory>定义的目录生效;
- Order参数如果添加在<Directory></Directory>之外,则是对serverName定义的虚拟主机网页生效。
例:针对server30.example.com下的/data目录网页只允许本机访问自己的网页,其他全拒绝:
[iyunv@server30 ~]# vim /etc/httpd/conf.d/httpd-vhosts.conf
6 # machine you can setup VirtualHost containers for them. Most configurations
8 # IP addresses. This is indicated by the asterisks in the directives below.
9 #
10 # Please see the documentation at
11 # <URL:http://httpd.apache.org/docs/2.4/vhosts/>
12 # for further details before you try to setup virtual hosts.
13 #
14 # You may use the command line option '-S' to verify your virtual host
15 # configuration.
16
17 #
18 # VirtualHost example:
19 # Almost any Apache directive may go into a VirtualHost container.
20 # The first VirtualHost section is used for all requests that do not
21 # match a ServerName or ServerAlias in any <VirtualHost> block.
22 #
23 <VirtualHost *:@@Port@@>
24 ServerAdmin webmaster@dummy-host.example.com
25 DocumentRoot "@@ServerRoot@@/docs/dummy-host.example.com"
26 ServerName dummy-host.example.com
27 ServerAlias www.dummy-host.example.com
28 ErrorLog "/var/log/httpd/dummy-host.example.com-error_log"
29 CustomLog "/var/log/httpd/dummy-host.example.com-access_log" common
30 </VirtualHost>
31
32 <VirtualHost *:@@Port@@>
33 ServerAdmin webmaster@dummy-host2.example.com
34 DocumentRoot "@@ServerRoot@@/docs/dummy-host2.example.com"
35 ServerName dummy-host2.example.com
36 ErrorLog "/var/log/httpd/dummy-host2.example.com-error_log"
37 CustomLog "/var/log/httpd/dummy-host2.example.com-access_log" common
38 </VirtualHost>
39
40 <VirtualHost 172.16.30.130:80>
41 ServerAdmin root@server30.example.com
42 DocumentRoot "/var/www/html"
43 <Directory "/var/www/html/data">
44 Options Indexes
45 Order deny,allow
46 deny from all
47 allow from 172.16.30.130
48 </Directory>
49 ServerName server30.example.com
50 ErrorLog "/var/log/httpd/server30.example.com-error_log"
51 CustomLog "/var/log/httpd/server30.example.com-access_log" common
52 </VirtualHost>
53
54 <VirtualHost 172.16.30.130:80>
55 ServerAdmin root@www.example.com
56 DocumentRoot "/var/www/virtual"
57 ServerName www.example.com
|
不要忘记重启服务
[iyunv@server30 ~]# systemctl restart httpd.service
|
desktop客户端访问验证
客户端访问拒绝。
Server30本机测试
访问成功。
4.8.2.Require参数
此参数是Redhat Linux7中Apache新添加的一个参数,在RHEL7中一般建议使用此参数。
注:
- Order参数如果添加在<Directory></Directory>之间,则是对<Directory>定义的目录生效;
- Order参数如果添加在<Directory></Directory>之外,则是对serverName定义的虚拟主机网页生效。
参数介绍:
允许所有人访问。
拒绝所有人
只允许172.16.30.130可以访问。
例1:使用Require参数,做到只允许desktop30可以访问server30的web网页下的data目录,server30自己也不可访问。
[iyunv@server30 ~]# vim /etc/httpd/conf.d/httpd-vhosts.conf
8 # IP addresses. This is indicated by the asterisks in the directives below.
9 #
10 # Please see the documentation at
11 # <URL:http://httpd.apache.org/docs/2.4/vhosts/>
12 # for further details before you try to setup virtual hosts.
13 #
14 # You may use the command line option '-S' to verify your virtual host
15 # configuration.
16
17 #
18 # VirtualHost example:
19 # Almost any Apache directive may go into a VirtualHost container.
20 # The first VirtualHost section is used for all requests that do not
21 # match a ServerName or ServerAlias in any <VirtualHost> block.
22 #
23 <VirtualHost *:@@Port@@>
24 ServerAdmin webmaster@dummy-host.example.com
25 DocumentRoot "@@ServerRoot@@/docs/dummy-host.example.com"
26 ServerName dummy-host.example.com
27 ServerAlias www.dummy-host.example.com
28 ErrorLog "/var/log/httpd/dummy-host.example.com-error_log"
29 CustomLog "/var/log/httpd/dummy-host.example.com-access_log" common
30 </VirtualHost>
31
32 <VirtualHost *:@@Port@@>
33 ServerAdmin webmaster@dummy-host2.example.com
34 DocumentRoot "@@ServerRoot@@/docs/dummy-host2.example.com"
35 ServerName dummy-host2.example.com
36 ErrorLog "/var/log/httpd/dummy-host2.example.com-error_log"
37 CustomLog "/var/log/httpd/dummy-host2.example.com-access_log" common
38 </VirtualHost>
39
40 <VirtualHost 172.16.30.130:80>
41 ServerAdmin root@server30.example.com
42 DocumentRoot "/var/www/html"
43 <Directory "/var/www/html/data">
44 Options Indexes
45 Require ip 172.16.30.30
46 </Directory>
47 ServerName server30.example.com
48 ErrorLog "/var/log/httpd/server30.example.com-error_log"
49 CustomLog "/var/log/httpd/server30.example.com-access_log" common
50 </VirtualHost>
51
52 <VirtualHost 172.16.30.130:80>
53 ServerAdmin root@www.example.com
54 DocumentRoot "/var/www/virtual"
55 ServerName www.example.com
56 ErrorLog "/var/log/httpd/www.example.com-error_log"
57 CustomLog "/var/log/httpd/www.example.com-access_log" common
58 </VirtualHost>
|
重启服务
[iyunv@server30 ~]# systemctl restart httpd.service
|
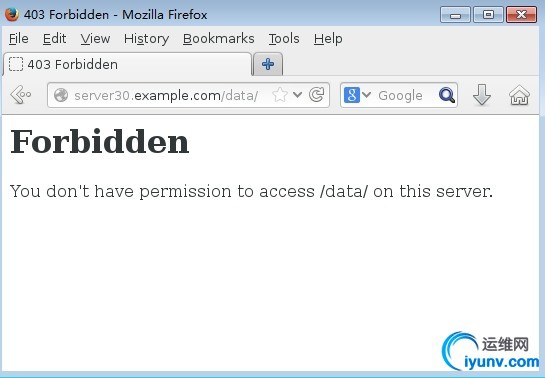
客户端访问
Server30自己访问自己的验证
访问拒绝。
例2:使用denied参数,拒绝所有人访问server30的web服务,包括自己
[iyunv@server30 ~]# vim /etc/httpd/conf.d/httpd-vhosts.conf
# machine you can setup VirtualHost containers for them. Most configurations
# use only name-based virtual hosts so the server doesn't need to worry about
# IP addresses. This is indicated by the asterisks in the directives below.
#
# Please see the documentation at
# <URL:http://httpd.apache.org/docs/2.4/vhosts/>
# for further details before you try to setup virtual hosts.
#
# You may use the command line option '-S' to verify your virtual host
# configuration.
#
# VirtualHost example:
19 # Almost any Apache directive may go into a VirtualHost container.
20 # The first VirtualHost section is used for all requests that do not
21 # match a ServerName or ServerAlias in any <VirtualHost> block.
22 #
23 <VirtualHost *:@@Port@@>
24 ServerAdmin webmaster@dummy-host.example.com
25 DocumentRoot "@@ServerRoot@@/docs/dummy-host.example.com"
26 ServerName dummy-host.example.com
27 ServerAlias www.dummy-host.example.com
28 ErrorLog "/var/log/httpd/dummy-host.example.com-error_log"
29 CustomLog "/var/log/httpd/dummy-host.example.com-access_log" common
30 </VirtualHost>
31
32 <VirtualHost *:@@Port@@>
33 ServerAdmin webmaster@dummy-host2.example.com
34 DocumentRoot "@@ServerRoot@@/docs/dummy-host2.example.com"
35 ServerName dummy-host2.example.com
36 ErrorLog "/var/log/httpd/dummy-host2.example.com-error_log"
37 CustomLog "/var/log/httpd/dummy-host2.example.com-access_log" common
38 </VirtualHost>
39
40 <VirtualHost 172.16.30.130:80>
41 ServerAdmin root@server30.example.com
42 DocumentRoot "/var/www/html"
43 <Directory "/var/www/html/data">
44 Options Indexes
45 Require all denied
46 </Directory>
47 ServerName server30.example.com
48 ErrorLog "/var/log/httpd/server30.example.com-error_log"
49 CustomLog "/var/log/httpd/server30.example.com-access_log" common
50 </VirtualHost>
51
52 <VirtualHost 172.16.30.130:80>
53 ServerAdmin root@www.example.com
54 DocumentRoot "/var/www/virtual"
55 ServerName www.example.com
56 ErrorLog "/var/log/httpd/www.example.com-error_log"
57 CustomLog "/var/log/httpd/www.example.com-access_log" common
58 </VirtualHost>
[iyunv@server30 ~]# systemctl restart httpd.service
|
客户端desktop30访问测试
Server30自己访问测试
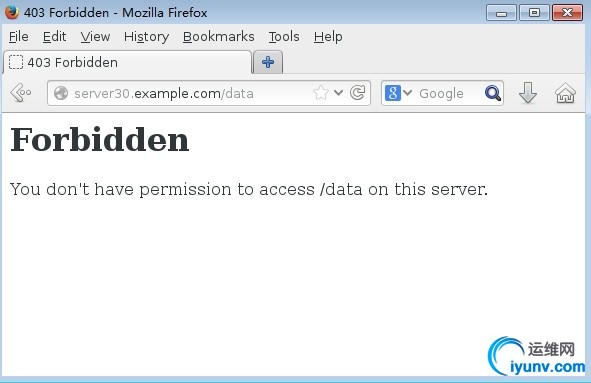
全部拒绝。
本部分实验完毕,请删除require参数规则,方便后面的实验。
4.9.目录身份验证
缺省情况下,Apache允许客户端的匿名访问。但也可实现基本身份验证(密码明文传输)和摘要身份验证(密码Hash算法加密)。本部分主要介绍基本身份验证。
使用基本身份验证,认证用户的来源可以使htpasswd工具生成的密码文件,可以是LDAP服务器上的,可以是MySQL内的用户,也可以是微软AD中的。本部分简单介绍第一种认证用户来源。
创建认证用户的密码文件
[iyunv@server30 ~]# htpasswd -cm /etc/httpd/.htpasswd user1
New password:
Re-type new password:
Adding password for user user1
[iyunv@server30 ~]# htpasswd -m /etc/httpd/.htpasswd user2
New password:
Re-type new password:
Adding password for user user2
[iyunv@server30 ~]# cat /etc/httpd/.htpasswd
user1:$apr1$qKhBbCLY$RJM5cCivDnJgAtyFazd1q/
user2:$apr1$V6c62hbd$C74QZ.QtlTMsN3LwzEavm.
|
说明:
- 此处的密码与系统定义的用户密码无关;
- -c为创建用户,-m为修改现有用户的密码。
修改配置文件,针对server30的/data目录进行目录身份认证
[iyunv@server30 ~]# vim /etc/httpd/conf.d/httpd-vhosts.conf
# If you want to maintain multiple domains/hostnames on your
# machine you can setup VirtualHost containers for them. Most configurations
# use only name-based virtual hosts so the server doesn't need to worry about
# IP addresses. This is indicated by the asterisks in the directives below.
#
# Please see the documentation at
# <URL:http://httpd.apache.org/docs/2.4/vhosts/>
# for further details before you try to setup virtual hosts.
#
# You may use the command line option '-S' to verify your virtual host
# configuration.
#
# VirtualHost example:
19 # Almost any Apache directive may go into a VirtualHost container.
20 # The first VirtualHost section is used for all requests that do not
21 # match a ServerName or ServerAlias in any <VirtualHost> block.
22 #
23 <VirtualHost *:@@Port@@>
24 ServerAdmin webmaster@dummy-host.example.com
25 DocumentRoot "@@ServerRoot@@/docs/dummy-host.example.com"
26 ServerName dummy-host.example.com
27 ServerAlias www.dummy-host.example.com
28 ErrorLog "/var/log/httpd/dummy-host.example.com-error_log"
29 CustomLog "/var/log/httpd/dummy-host.example.com-access_log" common
30 </VirtualHost>
31
32 <VirtualHost *:@@Port@@>
33 ServerAdmin webmaster@dummy-host2.example.com
34 DocumentRoot "@@ServerRoot@@/docs/dummy-host2.example.com"
35 ServerName dummy-host2.example.com
36 ErrorLog "/var/log/httpd/dummy-host2.example.com-error_log"
37 CustomLog "/var/log/httpd/dummy-host2.example.com-access_log" common
38 </VirtualHost>
39
40 <VirtualHost 172.16.30.130:80>
41 ServerAdmin root@server30.example.com
42 DocumentRoot "/var/www/html"
43 <Directory "/var/www/html/data">
44 Options Indexes
45 AuthName Test ①
46 AuthType basic ②
47 AuthUserFile /etc/httpd/.htpasswd ③
48 Require valid-user ④
49 </Directory>
50 ServerName server30.example.com
51 ErrorLog "/var/log/httpd/server30.example.com-error_log"
52 CustomLog "/var/log/httpd/server30.example.com-access_log" common
53 </VirtualHost>
54
55 <VirtualHost 172.16.30.130:80>
56 ServerAdmin root@www.example.com
57 DocumentRoot "/var/www/virtual"
58 ServerName www.example.com
59 ErrorLog "/var/log/httpd/www.example.com-error_log"
60 CustomLog "/var/log/httpd/www.example.com-access_log" common
|
①认证名,可以根据实际情况自定义
②认证类型,采用基本认证方式
③认证密码文件的路径
④指定认证密码文件中的所有用户均可以访问该目录,如果是require valid,则后面跟具体的用户(只有此用户可以访问)。
重启服务
[iyunv@server30 ~]# systemctl restart httpd.service
|
Desktop30客户端访问验证

①输入站点域名访问
②输入密码文件中的用户user1
③输入认证密码
访问成功。
User2访问测试
访问成功。
4.10.Web站点的TLS验证
Web站点的TLS验证,使用的就是HTTPS协议,实际生活中我们也是经常访问的。大多数敏感信息网站都是使用的HTTPS协议,如:淘宝、银行网站等。HTTPS协议保证了我们信息传送的安全性。
本部分实验我们以题目的形式来介绍,但是需要特定的环境,我们以自行搭建好了此环境。所以可以直接进行实验。如需特定环境,请实验者自行搭建。
题目:
前面我们已经介绍过,RHEL7中,Apache进行了简化安装,缺省没有安装模块。所以,要使用TLS加密,需要我们安装Apache的模块:mod_ssl,然后到/etc/httpd/conf.d/ssl.conf下面进行配置。
安装模块
[iyunv@server30 ~]# yum -y install mod_ssl
Loaded plugins: langpacks, product-id, subscription-manager
This system is not registered to Red Hat Subscription Management. You can use subscription-manager to register.
base | 4.1 kB 00:00
Resolving Dependencies
………………..
|
配置/etc/httpd/conf.d/ssl.conf文件
[iyunv@server30 ~]# cd /etc/httpd/conf.d/
[iyunv@server30 conf.d]# ll
total 36
-rw-r--r--. 1 root root 2893 Mar 20 2014 autoindex.conf
-rw-r--r--. 1 root root 2251 May 20 10:36 httpd-vhosts.conf
-rw-r--r--. 1 root root 295 Mar 20 2014 manual.conf
-rw-r--r--. 1 root root 366 Mar 20 2014 README
-rw-r--r--. 1 root root 9426 Mar 20 2014 ssl.conf
-rw-r--r--. 1 root root 1297 May 19 20:37 userdir.conf
-rw-r--r--. 1 root root 516 Mar 20 2014 welcome.conf
[iyunv@server30 conf.d]# vim ssl.conf
………………………..
100 SSLCertificateFile /etc/pki/tls/certs/localhost.crt
101
102 # Server Private Key:
103 # If the key is not combined with the certificate, use this
104 # directive to point at the key file. Keep in mind that if
105 # you've both a RSA and a DSA private key you can configure
106 # both in parallel (to also allow the use of DSA ciphers, etc.)
107 SSLCertificateKeyFile /etc/pki/tls/private/localhost.key
108
109 # Server Certificate Chain:
110 # Point SSLCertificateChainFile at a file containing the
111 # concatenation of PEM encoded CA certificates which form the
112 # certificate chain for the server certificate. Alternatively
113 # the referenced file can be the same as SSLCertificateFile
114 # when the CA certificates are directly appended to the server
115 # certificate for convinience.
116 #SSLCertificateChainFile /etc/pki/tls/certs/server-chain.crt
117
118 # Certificate Authority (CA):
119 # Set the CA certificate verification path where to find CA
120 # certificates for client authentication or alternatively one
121 # huge file containing all of them (file must be PEM encoded)
122 #SSLCACertificateFile /etc/pki/tls/certs/ca-bundle.crt
……….
|
打开配置文件,找到:
- 第100行:SSLCertificateFile /etc/pki/tls/certs/localhost.crt。针对签名证书的配置以及签名证书的路径;
- 第107行:SSLCertificateKeyFile/etc/pki/tls/private/localhost.key。针对证书密钥的配置及证书密钥的存放路径;
- 第122行:#SSLCACertificateFile /etc/pki/tls/certs/ca-bundle.crt。针对证书签名授权信息的配置及其存放路径。
我们要对此三行进行修改,改为我们题目说的文件名。当然,修改原则还是不修改模板,注释原有行(已注释的直接复制去注释修改),复制并修改
[iyunv@server30 conf.d]# vim ssl.conf
………………………..
100 #SSLCertificateFile /etc/pki/tls/certs/localhost.crt
101 SSLCertificateFile /etc/pki/tls/certs/server30.crt
102
103 # Server Private Key:
104 # If the key is not combined with the certificate, use this
105 # directive to point at the key file. Keep in mind that if
106 # you've both a RSA and a DSA private key you can configure
107 # both in parallel (to also allow the use of DSA ciphers, etc.)
108 #SSLCertificateKeyFile /etc/pki/tls/private/localhost.key
109 SSLCertificateKeyFile /etc/pki/tls/private/server30.key
110
111 # Server Certificate Chain:
112 # Point SSLCertificateChainFile at a file containing the
113 # concatenation of PEM encoded CA certificates which form the
114 # certificate chain for the server certificate. Alternatively
115 # the referenced file can be the same as SSLCertificateFile
116 # when the CA certificates are directly appended to the server
117 # certificate for convinience.
118 SSLCertificateChainFile /etc/pki/tls/certs/server-chain.crt
119
120 # Certificate Authority (CA):
121 # Set the CA certificate verification path where to find CA
122 # certificates for client authentication or alternatively one
123 # huge file containing all of them (file must be PEM encoded)
124 #SSLCACertificateFile /etc/pki/tls/certs/ca-bundle.crt
125 SSLCACertificateFile /etc/pki/tls/certs/group30.crt
……………
|
下载所需证书信息文件到指定路径
-----------------下载server30.crt和group30.crt-------------------
[iyunv@server30 conf.d]# cd /etc/pki/tls/certs/
[iyunv@server30 certs]# wget http://ldap.example.com/pub/server30.crt
--2015-05-20 11:03:29-- http://ldap.example.com/pub/server30.crt
Resolving ldap.example.com (ldap.example.com)... 172.16.30.254
Connecting to ldap.example.com (ldap.example.com)|172.16.30.254|:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 3147 (3.1K)
Saving to: ‘server30.crt’
100%[======================================>] 3,147 --.-K/s in 0s
2015-05-20 11:03:29 (284 MB/s) - ‘server30.crt’ saved [3147/3147]
[iyunv@server30 certs]# wget http://ldap.example.com/pub/group30.crt
--2015-05-20 11:05:23-- http://ldap.example.com/pub/group30.crt
Resolving ldap.example.com (ldap.example.com)... 172.16.30.254
Connecting to ldap.example.com (ldap.example.com)|172.16.30.254|:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 3256 (3.2K)
Saving to: ‘group30.crt’
100%[======================================>] 3,256 --.-K/s in 0s
2015-05-20 11:05:23 (209 MB/s) - ‘group30.crt’ saved [3256/3256]
[iyunv@server30 certs]# ls
ca-bundle.crt group30.crt make-dummy-cert renew-dummy-cert
ca-bundle.trust.crt localhost.crt Makefile server30.crt
------------------------下载server30.key--------------------
[iyunv@server30 certs]# cd /etc/pki/tls/private/
[iyunv@server30 private]# wget http://ldap.example.com/pub/server30.key
--2015-05-20 11:07:23-- http://ldap.example.com/pub/server30.key
Resolving ldap.example.com (ldap.example.com)... 172.16.30.254
Connecting to ldap.example.com (ldap.example.com)|172.16.30.254|:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 887
Saving to: ‘server30.key’
100%[======================================>] 887 --.-K/s in 0s
2015-05-20 11:07:23 (120 MB/s) - ‘server30.key’ saved [887/887]
[iyunv@server30 private]# ls
localhost.key server30.key
|
下载完成后,重启服务,防火墙允许https服务
[iyunv@server30 conf.d]# systemctl restart httpd.service
[iyunv@server30 data]# firewall-cmd --add-service=https --permanent
success
[iyunv@server30 data]# firewall-cmd --reload
success
|
客户端访问验证
①输入https://server.example.com的URL访问
②点击此处
为什么会出现此界面?
在Windows Server 2008服务中我们知道,下载向CA申请的证书之后,默认还要信任CA根证书,即要信任此CA机构,否则会报此界面的错误,提示CA证书不信任。如果确定是自己的CA,则可以继续按本实验步骤继续访问。
①点击此处添加例外
依次点击①②,完成例外网站的加载。显示内容,如下:
访问成功。此内容就是经过TLS加密之后使用HTTPS协议访问到的网站。
4.11.动态Web内容
本实验仍以题目的形式来试验。题目如下:
题目:
根据提示,建立虚拟主机
首先安装动态web’使用的模块
[iyunv@server30 wsgi]# yum -y install mod_wsgi
Loaded plugins: langpacks, product-id, subscription-manager
This system is not registered to Red Hat Subscription Management. You can use subscription-manager to register.
Resolving Dependencies
………………….
|
创建虚拟主机的DocumentRoot目录并下载索引文件
[iyunv@server30 ~]# mkdir /var/www/wsgi
[iyunv@server30 ~]# cd /var/www/wsgi
[iyunv@server30 wsgi]# wget http://ldap.example.com/pub/webapp.wsgi
--2015-05-20 13:09:33-- http://ldap.example.com/pub/webapp.wsgi
Resolving ldap.example.com (ldap.example.com)... 172.16.30.254
Connecting to ldap.example.com (ldap.example.com)|172.16.30.254|:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 277
Saving to: ‘webapp.wsgi’
100%[=========================================>] 277 --.-K/s in 0s
2015-05-20 13:09:33 (23.0 MB/s) - ‘webapp.wsgi’ saved [277/277]
[iyunv@server30 wsgi]# ls
webapp.wsgi
|
修改配置文件
[iyunv@server30 ~]# vim /etc/httpd/conf.d/httpd-vhosts.conf
…………………
Listen 890
<VirtualHost 172.16.30.130:8909>
ServerAdmin root@alt.example.com
WSGIScriptAlias / /var/www/wsgi/webapp.wsgi
ServerName alt.example.com:8909
ErrorLog "/var/log/httpd/alt.example.com-error_log"
CustomLog "/var/log/httpd/alt.example.com-access_log" common
</VirtualHost>
|
注:添加完虚拟主机不要忘记在DNS解析文件中添加虚拟主机的域名
修改SELinux,把此端口添加到内核信息,避免重打标签时失效
[iyunv@server30 wsgi]# semanage port -a -t http_port_t -p tcp 8909
|
添加防火墙策略,允许example.com这个域的访问。
[iyunv@server30 wsgi]# firewall-cmd --add-rich-rule "rule family=ipv4 source address=172.16.30.0/24 port port=8909 protocol=tcp accept" --permanent
success
[iyunv@server30 wsgi]# firewall-cmd --reload
Success
[iyunv@server30 wsgi]# firewall-cmd --list-all
public (default, active)
interfaces: eno16777736
sources:
services: dhcpv6-client http https ssh
ports:
masquerade: no
forward-ports:
icmp-blocks:
rich rules:
rule family="ipv4" source address="172.16.30.0/24" port port="8909" protocol="tcp" accept
|
重启服务,客户端访问测试
[iyunv@server30 wsgi]# systemctl restart httpd.service
|
注:访问时,URL后面一定要加上端口号,否则访问到的还是server30.example.com这个默认的网页内容。
|