|
|
在上一篇我们知道了,在不同的user account和workstations, 如何使用AES key去生成SecureString。我们需要去保护好Key,以免遭非法者解密数据保护。
在之前的例子中,我使用一个非常简单的16-byte 数组存储在脚本本身的主体。 这不是一个好的做法, 这和你密码用明文表示本质上是一样的。或者你可以在一个隔离的脚本里提前生成一个key。
作为一个例子,我已经建立了一个小脚本生成一个随机的16-byte数组。 我用System.Security.Cryptography.RNGCryptoServiceProvider 类随机生成的数据来填充一个字节数组。
Creating AES key with random data and export to file
1
2
3
4
| $KeyFile = "\SHSV2019SharePathAES.key"
$Key = New-Object Byte[] 16 #You can use 16, 24, or 32 for AES
[Security.Cryptography.RNGCryptoServiceProvider]::Create().GetBytes($Key)
$Key | Out-File $KeyFile
|
Creating SecureString object
1
2
3
4
5
| $PasswordFile = "\SHSV2019SharePathPassword.txt"
$KeyFile = "\SHSV2019SharePathAES.key"
$Key = Get-Content $KeyFile
# $Password = "P@ssword" | ConvertTo-SecureString -AsPlainText -Force
$Password | ConvertFrom-SecureString -Key $Key | Out-File $PasswordFile
|
Creating PSCredential object
1
2
3
4
5
| $User = "contosojason"
$PasswordFile = "\SHSV2019SharePathPassword.txt"
$KeyFile = "\SHSV2019SharePathAES.key"
$Key = Get-Content $KeyFile
$MyCredential = New-Object -TypeName System.Management.Automation.PSCredential -ArgumentList $User, (Get-Content $PasswordFile | ConvertTo-SecureString -Key $Key)
|
1. 加域脚本
1
2
3
4
5
6
| $User = "contosojason"
$PasswordFile = "\SHSV2019SharePathPassword.txt"
$KeyFile = "\SHSV2019SharePathAES.key"
$Key = Get-Content $KeyFile
$MyCredential = New-Object -TypeName System.Management.Automation.PSCredential -ArgumentList $User, (Get-Content $PasswordFile | ConvertTo-SecureString -Key $Key)
Add-Computer -DomainName contoso.com -Credential $MyCredential
|
将上面的加域脚本另存为"Joindomain.PS1"通过右键执行"Run with PowerShell"

执行后系统提示需要重启生效。
2. 退域脚本
1
2
3
4
5
6
| $User = "contosojason"
$PasswordFile = "\SHSV2019SharePathPassword.txt"
$KeyFile = "\SHSV2019SharePathAES.key"
$Key = Get-Content $KeyFile
$MyCredential = New-Object -TypeName System.Management.Automation.PSCredential -ArgumentList $User, (Get-Content $PasswordFile | ConvertTo-SecureString -Key $Key)
Remove-Computer -UnjoinDomainCredential $MyCredential -PassThru -Verbose -Restart
|
将上面退域脚本另存为"Unjoindomain.ps1",右键执行“Run with PowerShell”
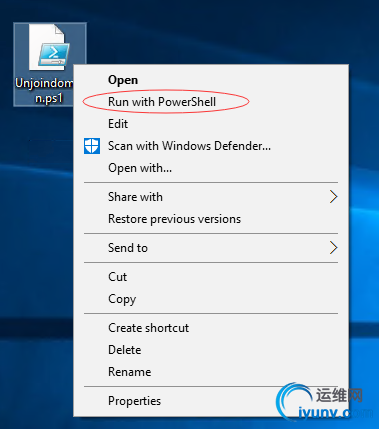
执行完毕,会自动重启,整个退域过程结束。
|
|